It was 2:47 a.m. when the first alert fired. By 4:00 a.m., 94% of the file infrastructure was locked. Their EDR had generated 34 alerts.
Every one was accurate.
Every one was useless.
A Decade of Assumptions – All Wrong
To understand how we got here, you have to understand what endpoint security was actually built for. The late 2000s and early 2010s were the golden age of signature-based security. Malware authors were lazy. They reused code, recycled infrastructure, and launched the same attack against a thousand targets using the same executable. The entire detection industry grew up around one central bet: if you have seen it before, you can stop it again.
And for a while, that bet paid off. Hashes were catalogued. IOCs were shared across industry groups. Signature packs updated daily, then hourly. The model worked because attackers gave it reasons to work. That era is over. And most of the industry has not caught up.
The AI Mutation Problem: Every Attack is New Code
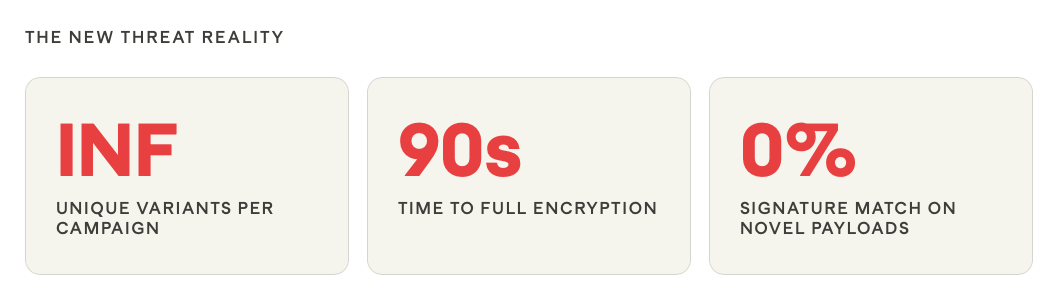
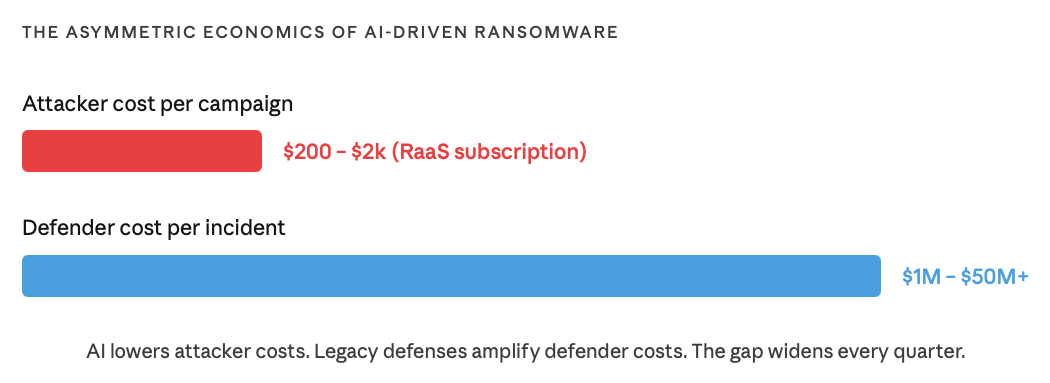
AI-assisted development tools, some purpose-built by criminal organizations, others adapted from legitimate software platforms, now allow ransomware operators to generate functionally identical but syntactically unique payloads at will. Every deployment can be a first-ever-seen file carrying a hash that has never appeared in any threat intelligence database.
This is not theoretical. Researchers have documented campaigns where operators generated hundreds of distinct payload variants for a single campaign. Not because they needed that many, but because the tooling made it essentially free.
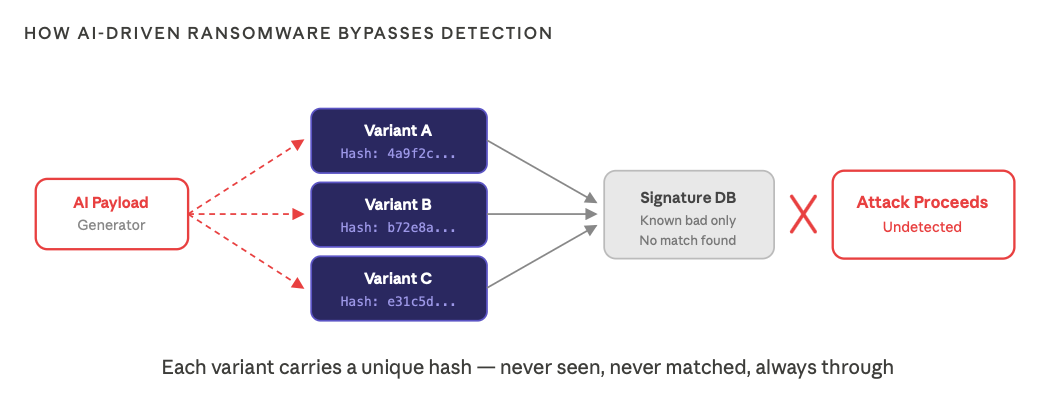
What this means in practice: encryption routines are randomized between deployments, runtime execution patterns shift, obfuscation layers are stacked, and living-off-the-land techniques mean there is often no malicious file to detect at all.
The EDR Myth: Detection Is Not Prevention
The security industry has spent years conflating detection capability with protection capability. EDR platforms are remarkable forensic tools, but calling EDR a prevention system is like calling a dashcam a seatbelt. The dashcam records everything. It did not stop the crash.
Mean time to respond is still measured in minutes or hours. Modern encryption routines complete their work in seconds. The gap between detection and response is not a process problem. It’s an architecture problem.
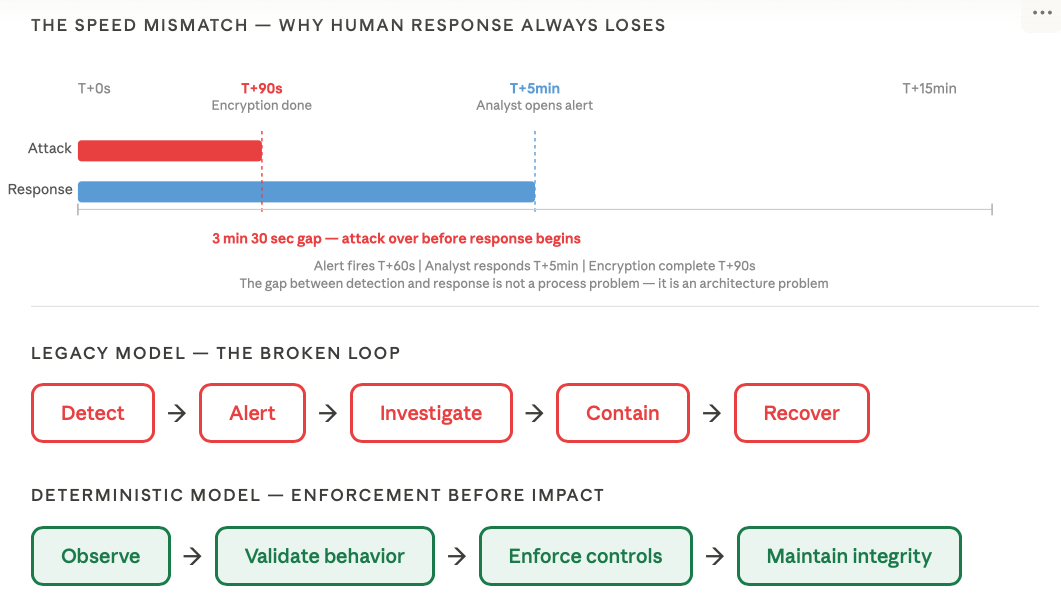
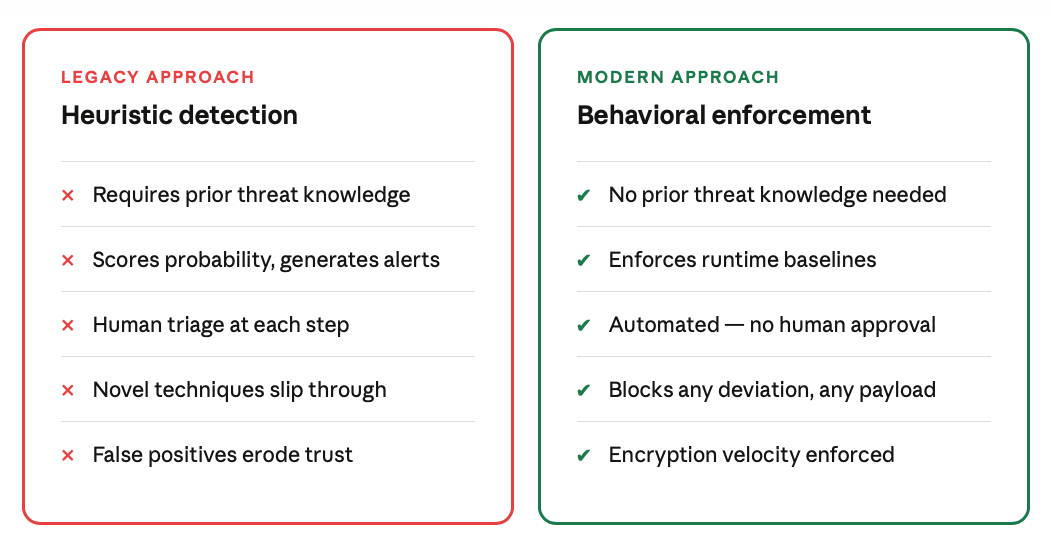
The Paradigm Shift: From Known Bad to Deterministic Behavioral Control
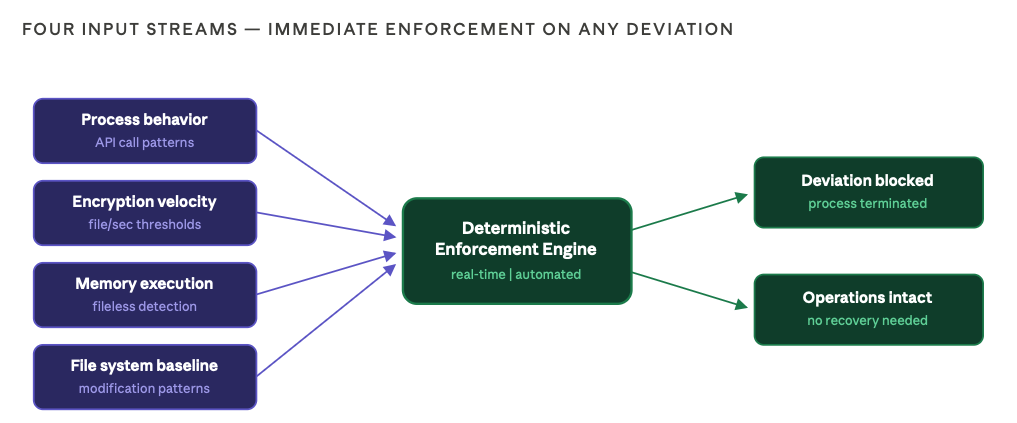
The old question was: is this file malicious? That question requires prior knowledge. The new question is: is this process behaving outside its deterministic operational boundaries? That requires only knowledge of what normal looks like and the authority to enforce it.
What Behavioral Enforcement Actually Monitors
The Business Case: What Boards Are Actually Asking
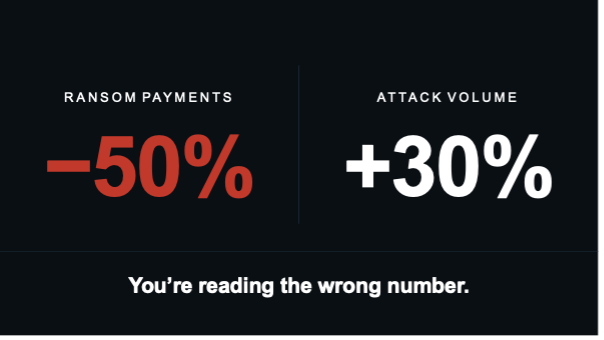
Boards have gotten smarter. They have lived through enough high-profile incidents – Colonial Pipeline, Change Healthcare, MGM Resorts – to understand that this is not an IT problem. It is an operational risk problem, a revenue risk problem.
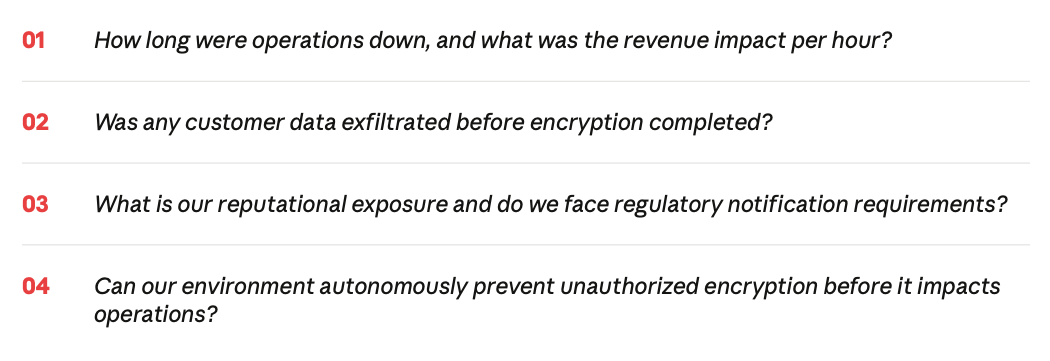
Not one of those questions is: did we detect it? Detection is a consolation prize. Boards have internalized that cybersecurity is no longer about blocking threats. It’s about staying operational under attack.
“We had 34 alerts and 73 minutes and we still lost. The problem was not that we did not know. The problem was that knowing was not enough.” – CISO, logistics company
Conclusion: Resilience Is the New Perimeter
Signature-based ransomware detection is not failing because of poor implementation or underfunding. It is structurally obsolete against AI-driven mutation.
“Do we have EDR?” is the wrong question. The right question is “Can our environment autonomously prevent encryption before it impacts operations?”
The future is deterministic, behavioral enforcement that requires no prior knowledge, no human approval cycle, and no post-compromise recovery as the primary defense.
Jason T. Williams is the Senior Director of Global Solutions Architecture at Arms Cyber. Our patented Stealth Posture Management platform protects organizations across Windows, Linux, and MacOS by making critical data invisible and resilient to attackers.