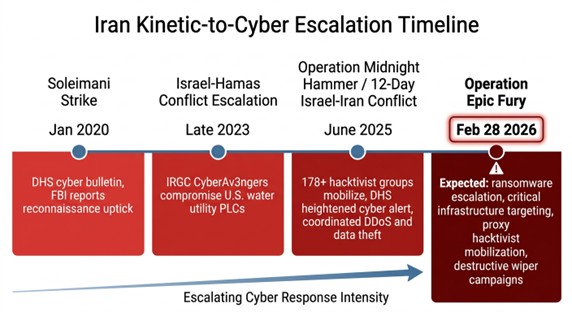
As of this past weekend, the United States and Israel have launched Operation Epic Fury, a coordinated, large-scale military campaign against Iranian military infrastructure, nuclear facilities, and regime targets. Explosions have been reported across Tehran, Isfahan, Qom, Karaj, and Kermanshah. Iran has already retaliated with ballistic missiles targeting U.S. bases across the Persian Gulf and Israeli territory. The conflict is active and escalating.
This piece is not about the geopolitics of the strikes themselves. It’s about what comes next in a domain that won’t wait for a ceasefire: cyberspace. If history is any guide, and the pattern here is remarkably consistent, U.S. organizations, particularly those in critical infrastructure, defense, healthcare, finance, and local government, should be preparing right now for a significant escalation in Iranian-linked cyber operations, including ransomware.
This is not speculation. It’s the playbook Iran has run every single time kinetic tensions rise, and every indicator suggests they’re running it again.
Iran’s Cyber Doctrine: Asymmetric Retaliation at Scale
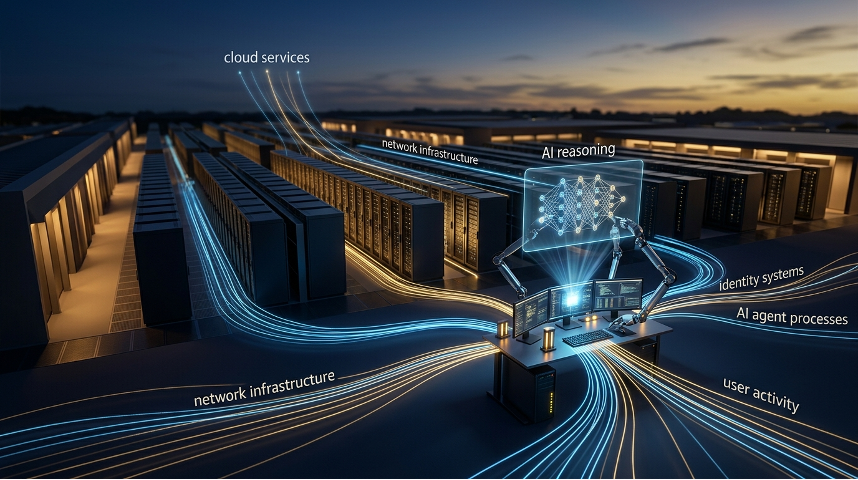
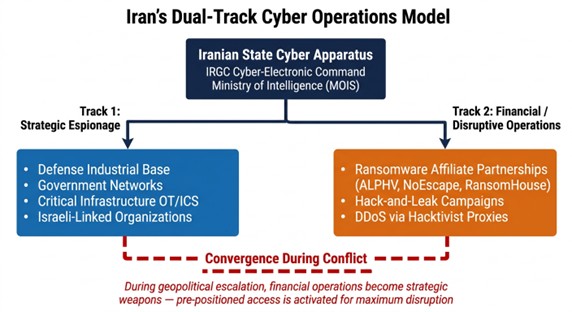
Iran has long understood that it cannot match the United States in conventional military power. Its national security strategy is built around asymmetric capabilities, proxy networks, maritime disruption, and increasingly, offensive cyber operations. When kinetic pressure escalates, cyber retaliation has consistently followed, not as a secondary concern, but as a primary instrument of strategic response.
The pattern is well documented. After the U.S. killing of IRGC General Qasem Soleimani in January 2020, DHS issued an immediate bulletin warning that Iran could execute cyberattacks against U.S. critical infrastructure with little or no warning [1]. The FBI observed a measurable uptick in Iranian cyber reconnaissance activity within days [2]. When the Israel-Hamas conflict escalated in late 2023, IRGC-affiliated actors compromised Israeli-made programmable logic controllers and human-machine interfaces deployed at dozens of U.S. water and wastewater facilities [3]. During last June’s twelve-day Israel-Iran conflict and Operation Midnight Hammer, DHS again warned of heightened cyber risk [4][5], and analysis of over 250,000 Telegram messages from more than 178 hacktivist and proxy groups revealed coordinated, rapid mobilization of Iranian-backed cyber campaigns timed to military operations [6][7].
The escalation happening today dwarfs all of those precedents. Operation Epic Fury is not a limited strike, it is a sustained campaign that the U.S. has described as targeting Iran’s missile capabilities, military infrastructure, and the regime itself. For a nation that treats cyber operations as a core asymmetric tool, this level of kinetic pressure virtually guarantees a corresponding escalation in cyber activity against U.S. targets.
Former DHS Deputy Assistant Secretary Tom Warrick put it plainly in his Atlantic Council assessment: this war will have a home front in the United States, and Iran will try every cyber operation it can mount [8].
The Ransomware Connection Most People Miss
When people think of Iranian cyber threats, they tend to picture state-sponsored espionage groups conducting targeted intrusions against defense contractors and government agencies. That picture is accurate, but it’s incomplete. One of the most consequential developments in the Iranian cyber threat landscape over the past two years has been the deepening collaboration between Iranian state-linked actors and criminal ransomware operations.
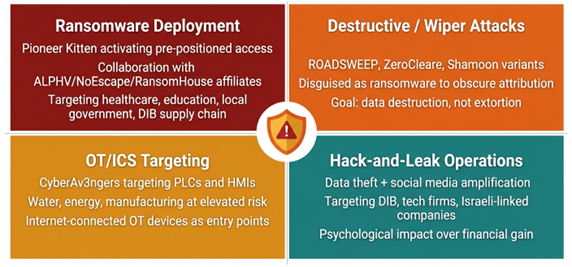
The group tracked as Pioneer Kitten, also known as Fox Kitten, Lemon Sandstorm, and RUBIDIUM, exemplifies this convergence. A joint advisory from the FBI, CISA, and the Department of Defense Cyber Crime Center documented that Pioneer Kitten, an IRGC-connected threat group, has been actively collaborating with ransomware affiliates including ALPHV/BlackCat, NoEscape, and RansomHouse [9]. Their involvement goes beyond simply selling access. These actors work directly with ransomware operators to lock down victim networks and develop extortion strategies, all while concealing their Iranian origin from their criminal partners.
The sectors they’ve targeted include healthcare, education, finance, defense, and local government, precisely the organizations least equipped to absorb a ransomware attack and most likely to pay. The FBI assesses that a significant percentage of Pioneer Kitten’s operations against U.S. organizations are specifically intended to develop and maintain network access for future ransomware deployment.
This matters enormously in the current context. Iranian state-sponsored groups have historically operated on two tracks simultaneously: intelligence collection in support of the regime’s geopolitical interests, and financially motivated operations that fund their activities and inflict economic damage. When kinetic conflict escalates, the incentive structure shifts. Operations that were previously conducted opportunistically can be directed strategically. Network access that was being quietly maintained for future ransomware deployment can be activated on command.
The Hacktivist Ecosystem Is Not What It Seems
One of the most dangerous misconceptions about Iranian cyber operations is that the hacktivist groups associated with Tehran, CyberAv3ngers, Fatimion Cyber Team, Cyber Fattah, Cyber Islamic Resistance, and dozens of others, are unsophisticated opportunists conducting nuisance-level attacks. The reality, as documented by CSIS and multiple U.S. intelligence agencies, is that these groups operate as a coordinated ecosystem with institutional backing from the Iranian state.
During last June’s twelve-day conflict, researchers analyzed the hacktivist response and found patterns in attack timing, target selection, and the exchange of vulnerabilities and attack scripts across groups that indicated orchestration, not organic activity. Iran uses this ecosystem strategically: when it needs deniability and widespread disruption, it activates hacktivist personas; when it needs sophisticated access and precision targeting, it deploys APT groups. The same resources, intelligence, and sometimes infrastructure flow between them.
This matters for U.S. organizations because the initial wave of cyber retaliation is likely to come from these hacktivist proxies, DDoS campaigns against public-facing services, website defacements, data theft and leak operations designed for maximum psychological impact. These attacks may seem relatively unsophisticated in isolation, but they serve multiple purposes: they generate headlines, they strain incident response resources, and they provide cover for more targeted operations happening simultaneously further up the sophistication stack.
The joint advisory from CISA, FBI, DC3, and NSA issued after Operation Midnight Hammer last June explicitly warned that Iranian state-sponsored actors would likely significantly increase DDoS campaigns and potentially conduct ransomware attacks. Every condition that prompted that warning has now been amplified by an order of magnitude [5].
What U.S. Organizations Should Expect
Based on Iran’s documented capabilities, established partnerships, and historical escalation patterns, organizations should be preparing for several concurrent threat streams.
Ransomware deployment against soft targets. Healthcare systems, school districts, municipal governments, water utilities, and small-to-midsize businesses in the defense supply chain are all likely targets. Iranian actors have pre-positioned access in many of these environments by exploiting known vulnerabilities in VPN appliances, firewalls, and remote access tools. Access that has been sitting dormant may now be activated.
Destructive attacks disguised as ransomware. Iran has a documented history of deploying wiper malware, including ROADSWEEP, ZeroCleare, and Shamoon variants, under the guise of ransomware operations. The goal of these attacks is not financial; it’s to destroy data and disrupt operations while creating the appearance of a criminal attack. In the current environment, organizations that experience a ransomware event should consider the possibility that data recovery may not be the attacker’s intended outcome.
Attacks on operational technology and industrial control systems. The IRGC’s CyberAv3ngers group has already demonstrated the capability and willingness to target Israeli-manufactured PLCs and HMIs deployed in U.S. critical infrastructure. Water treatment facilities, energy distribution systems, and manufacturing environments that rely on internet-connected OT devices are at elevated risk.
Hack-and-leak operations. Iranian actors have repeatedly combined data theft with information operations — stealing sensitive data and then publicizing the breach through social media and dedicated leak sites to maximize reputational and psychological damage. Defense contractors, technology.
What To Do Right Now
This is not a theoretical exercise. The kinetic operations underway today will generate cyber consequences in the days and weeks ahead, and potentially much sooner. Some recommendations for immediate action.
Patch aggressively, starting with edge devices. Iranian actors exploit known vulnerabilities in internet-facing devices faster than most organizations patch them. If you have unpatched appliances, assume they may already be compromised and investigate accordingly. CISA’s Known Exploited Vulnerabilities catalog is a good starting point for prioritization.
Audit your VPN and remote access infrastructure. Pioneer Kitten’s entire initial access methodology revolves around exploiting remote access tools. Verify that default credentials have been changed, MFA is enforced on all remote access, and that you have visibility into authentication logs for anomalous patterns — particularly brute force attempts and password spraying.
Assume pre-positioned access exists. If your organization runs any of the products on the known CVE list exploited by Iranian actors [10], conduct a proactive hunt for indicators of compromise. Don’t rely on your existing detection tools alone — look for web shells, unauthorized accounts, unusual lateral movement, and unexpected outbound connections.
Ensure your backups are offline and tested. In a wiper scenario disguised as ransomware, your backups are the only path to recovery. Verify that backup infrastructure is segmented from your production environment and that restoration has been tested recently. If your backup strategy depends on cloud-connected or network-accessible storage, it is vulnerable. Immutable backup solutions are another alternative to this to ensure that backups are not corrupted in the event that an air gapped environment can not be created. However, it is important to ensure that an integrity monitoring mechanism is implemented to checkpoint the last legitimate backup before the malware has taken effect.
Brief your teams and update your incident response plans. Make sure your SOC, IT operations, and executive leadership understand the elevated threat environment. If you use a managed security provider, confirm that they have updated their detection rules and monitoring posture for Iranian TTPs. If you have an incident response retainer, verify that it’s active and that your provider is prepared for surge demand.
Segment your OT environments. If you operate industrial control systems, ensure they are not directly accessible from the internet and that IT-OT network segmentation is in place. Iranian actors specifically target environments where OT devices are reachable from corporate networks.
The Bigger Picture
What we’re witnessing today is the latest and most dramatic demonstration of a trend that has been building for years: kinetic conflict and cyber operations are no longer separate domains. They are fused. Military strikes generate cyber retaliation. Cyber operations enable military campaigns, as we saw when U.S. Cyber Command reportedly disrupted Iranian air defense systems during last June’s Operation Midnight Hammer. The attack surface for nation-state conflict now extends directly into the networks of private companies, hospitals, school districts, and water utilities that have no direct connection to the battlefield but plenty of connection to the internet.
Iran’s conventional military capabilities are being degraded by the strikes underway today. Its cyber capabilities are not. The IRGC’s cyber units, the hacktivist proxy network, the ransomware affiliate partnerships, and the pre-positioned access sitting in U.S. networks, none of these are affected by airstrikes. If anything, the destruction of conventional capability increases the regime’s reliance on asymmetric tools, and cyber is the most powerful asymmetric tool they possess.
The organizations that will weather this period are not the ones that react after the breach. They’re the ones that are patching their edge devices today, hunting for pre-positioned access today, testing their backups today, and briefing their teams today. The threat is not hypothetical. It’s not even imminent. It’s here.
Brad Potteiger is the Chief Technology Officer at Arms Cyber, where he leads the development of next-generation preemptive security and anti-ransomware technology. Arms Cyber’s patented Stealth Posture Management platform protects organizations across Windows, Linux, and macOS by making critical data invisible and resilient to attackers — a prevention-layer control designed to neutralize ransomware before it can encrypt.
References
[1] DHS NTAS Bulletin, January 4, 2020
https://www.dhs.gov/ntas/advisory/national-terrorism-advisory-system-bulletin-january-4-2020
[2] NPR, “U.S. Government Officials And Security Experts Warn Of Iran Cyberthreat,” January 21, 2020
https://www.npr.org/2020/01/21/797449708/iran-conflict-could-shift-to-cyberspace-experts-warn
[3] CISA Joint Advisory AA23-335A, “IRGC-Affiliated Cyber Actors Exploit PLCs in Multiple Sectors, Including U.S. Water and Wastewater Systems Facilities,” December 1, 2023 (updated December 18, 2024)
https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-335a
[4] DHS NTAS Bulletin, June 22, 2025
https://www.dhs.gov/ntas/advisory/national-terrorism-advisory-system-bulletin-june-22-2025
[5] CISA/FBI/DC3/NSA Joint Fact Sheet, “Iranian Cyber Actors May Target Vulnerable US Networks and Entities of Interest,” June 30, 2025
https://media.defense.gov/2025/Jun/30/2003745375/-1/-1/0/JOINT-FACT-SHEUQDgwqVE-6aMBLYLbQv6i5N5y7bC5SajqSjHPzt8UJUqbZ8a-NETWORKS-AND-ENTITIES-OF-INTEREST-508C.PDF
[6] SecurityScorecard STRIKE Report, “From the Depths of the Shadows: IRGC and Hacker Collectives of the 12-Day War,” August 2025
https://securityscorecard.com/blog/from-the-depths-of-the-shadows-irgc-and-hacker-collectives-of-the-12-day-war/
[7] CSIS, “Beyond Hacktivism: Iran’s Coordinated Cyber Threat Landscape”
https://www.csis.org/blogs/strategic-technologies-blog/beyond-hacktivism-irans-coordinated-cyber-threat-landscape
[8] Atlantic Council, “Experts React: The US and Israel Just Unleashed a Major Attack on Iran. What’s Next?,” February 28, 2026 https://www.atlanticcouncil.org/dispatches/experts-react-the-us-and-israel-just-unleashed-a-major-attack-on-iran-whats-next/
[9] FBI/CISA/DC3 Joint Advisory AA24-241A, “Iran-based Cyber Actors Enabling Ransomware Attacks on US Organizations,” August 28, 2024 https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-241a
[10] CISA, “Iran Threat Overview and Advisories” (aggregated list of all Iranian-attributed advisories, CVEs, IOCs, and TTPs) https://www.cisa.gov/topics/cyber-threats-and-advisories/advanced-persistent-threats/iran