If you’ve spent any time talking to CISOs in the last two years, you’ve heard some version of the same frustration: “We have too many tools and not enough people to run them.” It’s become the defining tension of modern cybersecurity. And it’s driving a debate that, in my view, the industry is framing wrong.
The conversation usually gets reduced to a binary: should we buy products or buy services? Do we invest in technology or outsource to an MSSP? The reality is that this is a false choice, and organizations that treat it as an either/or question end up with the worst of both worlds. To get the answer right, you first have to understand what each model is designed to deliver, where each breaks down, and why the real question is about the architecture of your security technology stack, not procurement.
What products give you (and what they don’t)
Cybersecurity products, your EDR agents, SIEM platforms, firewalls, vulnerability scanners, identity tools, are fundamentally about capability. They give your organization the ability to detect, prevent, or respond to specific categories of threats. A well-chosen product does a defined job, often extremely well.
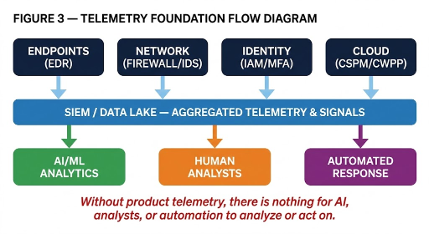
The appeal is obvious. Products scale. Once deployed, an endpoint agent protects every machine it’s installed on without adding headcount. Products are deterministic, they apply policy consistently, around the clock, without the variability you get from human analysts on different shifts. And products represent a capital investment you own and control, which matters to organizations that are rightly cautious about handing their security posture to a third party. Critically, products also form the telemetry foundation of your entire security program: without deployed products generating logs, alerts, and signals, there is nothing for analysts, human or AI, to review, correlate, or act on.
But products have inherent limitations that the industry has been slow to address. The first is operational burden. Every product requires care and feeding: configuration, tuning, integration, patching, and ongoing administration. Research from IBM and the Ponemon Institute found that the average enterprise now juggles 83 different security solutions from 29 vendors (IBM/Ponemon, “Cost of a Data Breach Report,” 2023). That’s not a security architecture. It’s a maintenance nightmare. Sixty-five percent of organizations say they have too many security tools, and over half report that their tools can’t be properly integrated with each other.
The second limitation is that products don’t think. A tool can generate an alert, but it can’t determine whether that alert matters in the context of your specific environment, your business operations, or the threat actor’s broader campaign. That judgment requires human expertise, and it’s the piece that makes the difference between generating noise and measurably reducing risk.
The third, and this is the one I think about most, is that products are inherently reactive to the threat landscape they were designed for. When the threat model shifts, which it is doing dramatically right now as AI reshapes offensive operations, products built around yesterday’s assumptions develop blind spots. Traditional signature-based detection and even ML-based static analysis models trained on pre-AI malware struggle against the polymorphic and AI-generated threats emerging today. Behavioral detection fares better, since there are only so many ways to perform actions like reading and writing files regardless of who or what writes the malware. But the overall detection stack still needs continuous evolution to keep pace with AI-accelerated offense. The product still functions perfectly; it just may not be solving the right problem anymore.
What services give you (and what they don’t)
Security services, MSSPs, MDR providers, SOC-as-a-Service, incident response retainers, are fundamentally about capacity and expertise. They give your organization access to skilled human analysts, mature operational processes, and 24/7 coverage that most companies simply cannot build or afford in-house.
This matters enormously in the current environment. The global cybersecurity workforce gap stands at roughly 4.8 million unfilled positions. Building an internal SOC that operates around the clock, with the depth of expertise needed to handle sophisticated threats, is effectively impossible for all but the largest enterprises. Services fill that gap, and for many organizations, they’re the only realistic path to meaningful security operations.
The best managed services providers bring something else that’s hard to replicate internally: pattern recognition across a broad client base. An MDR provider monitoring hundreds of environments sees attack patterns, emerging tactics, and novel threat behaviors at a scale that no single organization’s team can match. That collective intelligence is genuinely valuable and allows them to craft better response plans as they see the same attacks across their customer base.
But services have their own structural limitations. The most fundamental is the ownership gap. When you outsource your security operations, you’re trusting that a third party cares about your environment as much as you do. In practice, MSSPs and MDR providers are managing dozens or hundreds of clients simultaneously. Rotating analysts may lack institutional knowledge of your specific infrastructure, business processes, and risk profile. When an incident occurs, the accountability still rests with you — the service provider detects and notifies, but you bear the consequences of a breach.
There’s also the depth-versus-breadth tradeoff. Many MSSPs provide broad monitoring across common security categories but lack deep specialization in any one area. They’re excellent at processing the alert volume that overwhelms internal teams, but they may not have the expertise to handle the specific threats that matter most to your organization. As CrowdStrike has pointed out, the difference between MSSP and MDR is significant, one manages and monitors, while the other actively hunts and responds, and the distinction is often blurred in vendor marketing.
Finally, services can become a crutch that prevents organizations from building the internal capabilities they require. If your security knowledge lives entirely inside a third party’s SOC, you’ve created a dependency that’s difficult and expensive to unwind, and you’ve lost the ability to make informed decisions about your own risk posture.
The question nobody’s asking correctly
Here’s where the industry’s framing goes wrong. The debate between products and services is really a debate about two complementary dimensions of security: what your organization is capable of doing versus whether you have the capacity to do it effectively. You need both. The question isn’t which one to choose, it’s how to architect your security program so that the right capabilities are in place and the right operational model ensures they function correctly.
This is where I see organizations making the most consequential mistakes. They stack products without an operational model to support them, ending up with the tool sprawl problem that’s become almost universal. Or they outsource everything to a services provider without ensuring the underlying technology stack is solving the right problems, essentially paying for 24/7 monitoring of tools that are missing the threats that matter.
The organizations I see getting this right tend to share a few characteristics. First, they start with a threat model, not a vendor catalog. Before buying a product or signing a services contract, they’ve clearly defined what they’re defending against, what the likely attack vectors are, and where their current defenses have genuine gaps. This sounds basic, but it’s remarkable how often technology and service decisions are driven by sales cycles or peer pressure rather than a rigorous risk assessment.
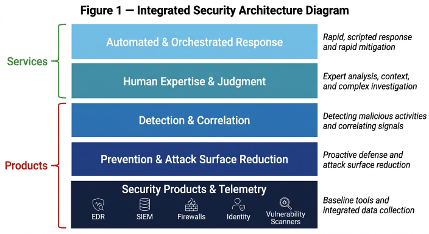
Second, successful security programs think in layers, not categories. The most resilient security architectures combine prevention technologies that reduce the attack surface proactively, detection capabilities that identify threats that get through, human expertise that provides judgment and context, and automated response that acts faster than manual processes allow. Products and services aren’t alternatives within these layers. They’re different delivery mechanisms for capabilities that every layer requires.
Third, they accept that the mix will change over time. An early-stage company with no security team and a handful of endpoints has different needs than a mature enterprise with a dedicated SOC. The right balance of products and services isn’t static. It evolves with the organization’s size, risk profile, regulatory environment, and internal capabilities. What matters is having a deliberate strategy rather than accumulating point solutions and service contracts reactively.
Where this all gets harder
Two converging trends are making this calculus more complex and more consequential than it’s ever been.
The first is the AI-induced transformation of the threat landscape. As AI-driven attacks become faster, more adaptive, and harder to detect using traditional methods, both products and services need to evolve. Products need to incorporate proactive defense mechanisms, such as deception technology, runtime application self-protection (RASP), and automated attack surface management, that don’t depend on recognizing the attack after it’s arrived. Services need analysts and automation that can operate at machine speed, not human speed. The old model of “detect alert, create ticket, wait for analyst” breaks down when attacks compress the entire kill chain into minutes.
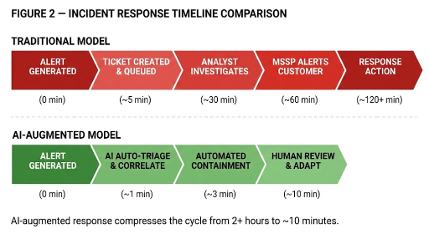
The second is the AI transformation of security operations themselves. AI-driven SOC platforms are beginning to automate significant portions of what human analysts have traditionally done: triaging alerts, correlating signals, enriching incidents, and recommending responses. This is reshaping the economics of the product-versus-service decision in real time. If AI can handle Tier-1 triage internally, the argument for outsourcing that function to an MSSP weakens. But the need for human expertise at the strategic and investigative level becomes even more critical, and harder to hire for. Crucially, these AI platforms are not standalone: they require rich telemetry and signal data from deployed security products to function. Without the right product foundation generating high-fidelity data, even the most sophisticated AI-driven SOC platform has nothing meaningful to analyze.
Getting the architecture right
If I could leave security leaders with one message, it’s this: stop asking “should I buy products or services?” and start asking “do I have the right architectural foundation, and do I have the right operational model to make it work?”
The correct architecture starts with a telemetry-rich product foundation that provides comprehensive visibility across endpoints, network, identity, and cloud. On top of that foundation sits a detection and correlation layer, increasingly AI-augmented, that transforms raw signals into prioritized, actionable intelligence. Human expertise, whether internal or delivered through managed services, provides the judgment, context, and strategic direction that machines cannot. And automated response capabilities ensure that when threats are identified, containment happens at machine speed, not calendar speed. Each of these layers must be deliberately chosen and integrated, not accumulated piecemeal.
The organizations that will weather the coming threat landscape aren’t the ones with the most products deployed or the most expensive MSSP contract. They’re the ones with a security architecture that’s deliberately designed, where each layer serves a clear purpose, where technology and human expertise reinforce each other, and where the overall program can adapt as threats, regulations, and organizational needs evolve.
Products without operational expertise are shelfware. Services without the right technology foundation are expensive false confidence. The answer has always been both…but “both” only works when it’s designed, not accumulated.
Brad Potteiger is the Chief Technology Officer at Arms Cyber, where he leads the development of next-generation preemptive security & anti-ransomware technology. Arms Cyber’s patented Stealth Posture Management platform protects organizations across Windows, Linux, and MacOS by making critical data invisible and resilient to attackers.