Next week, roughly 44,000 cybersecurity professionals will descend on San Francisco’s Moscone Center for RSAC 2026 Conference — the industry’s largest and most influential annual gathering, now celebrating its 35th year. The theme this year is “The Power of Community,” inspired by the African proverb: If you want to go quickly, go alone. If you want to go far, go together.
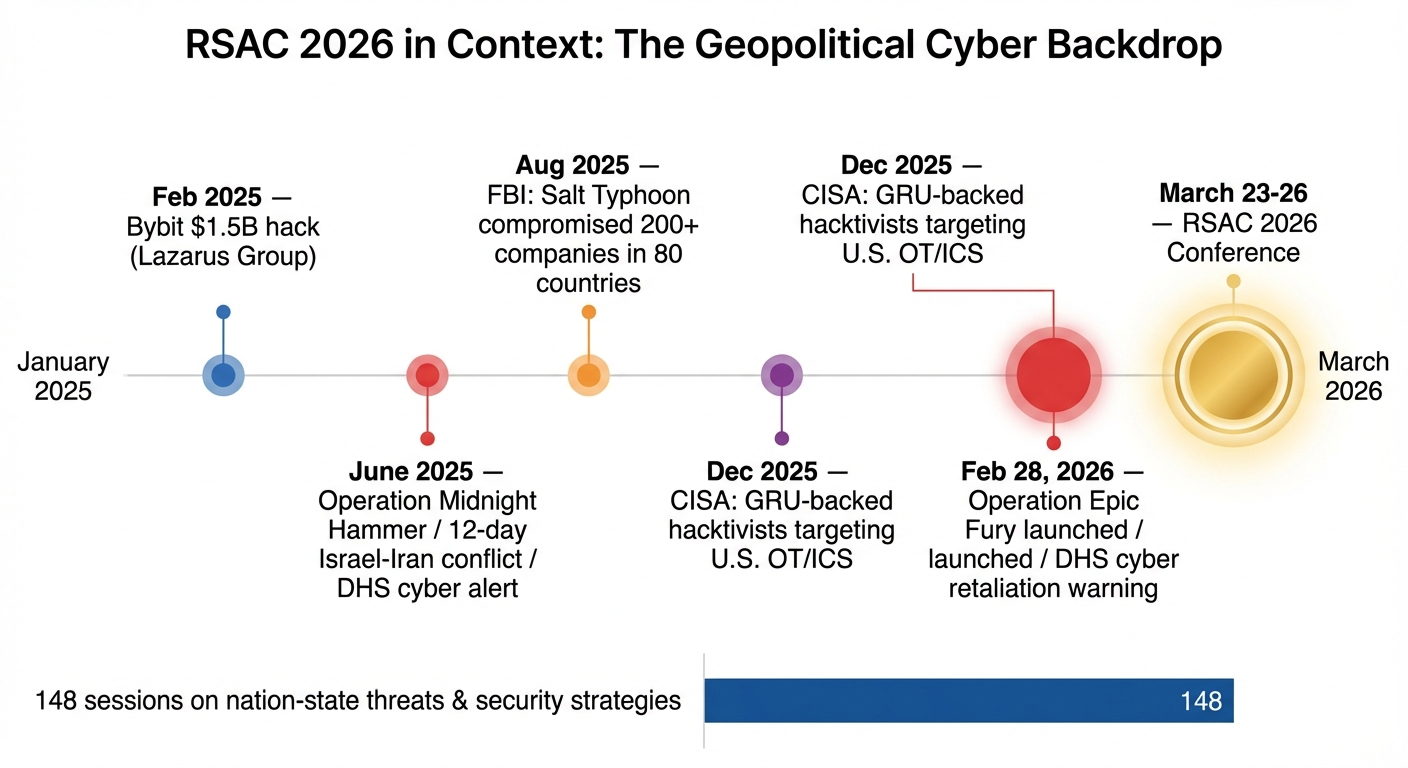
It’s a fitting frame for a conference that arrives at a moment of extraordinary convergence. The geopolitical landscape has intensified dramatically — Operation Epic Fury launched against Iran, the Typhoon campaigns from China continue to reshape how we think about critical infrastructure risk, and North Korea’s Lazarus Group stole over $2 billion in cryptocurrency in 2025 alone. Meanwhile, the technology powering both offense and defense is undergoing its most fundamental shift since the advent of cloud computing.
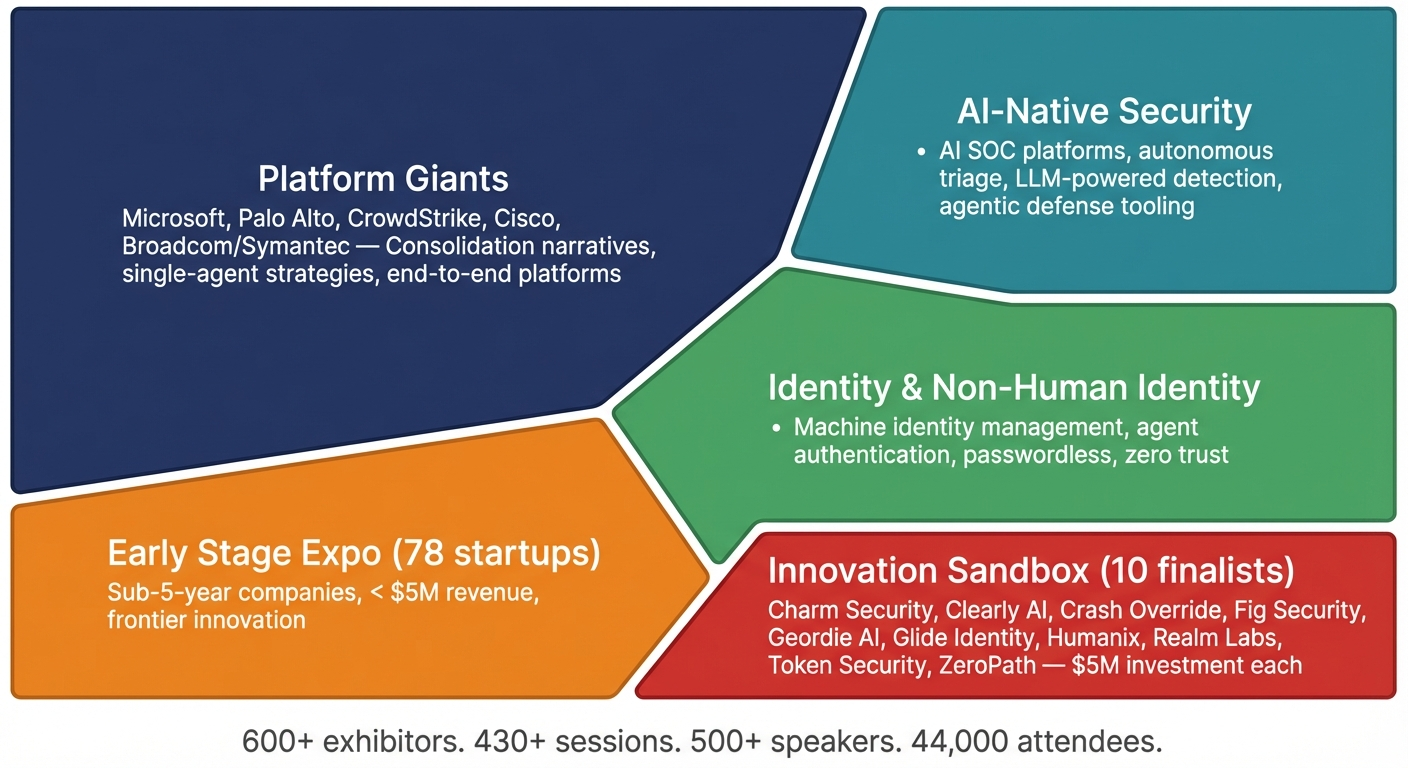
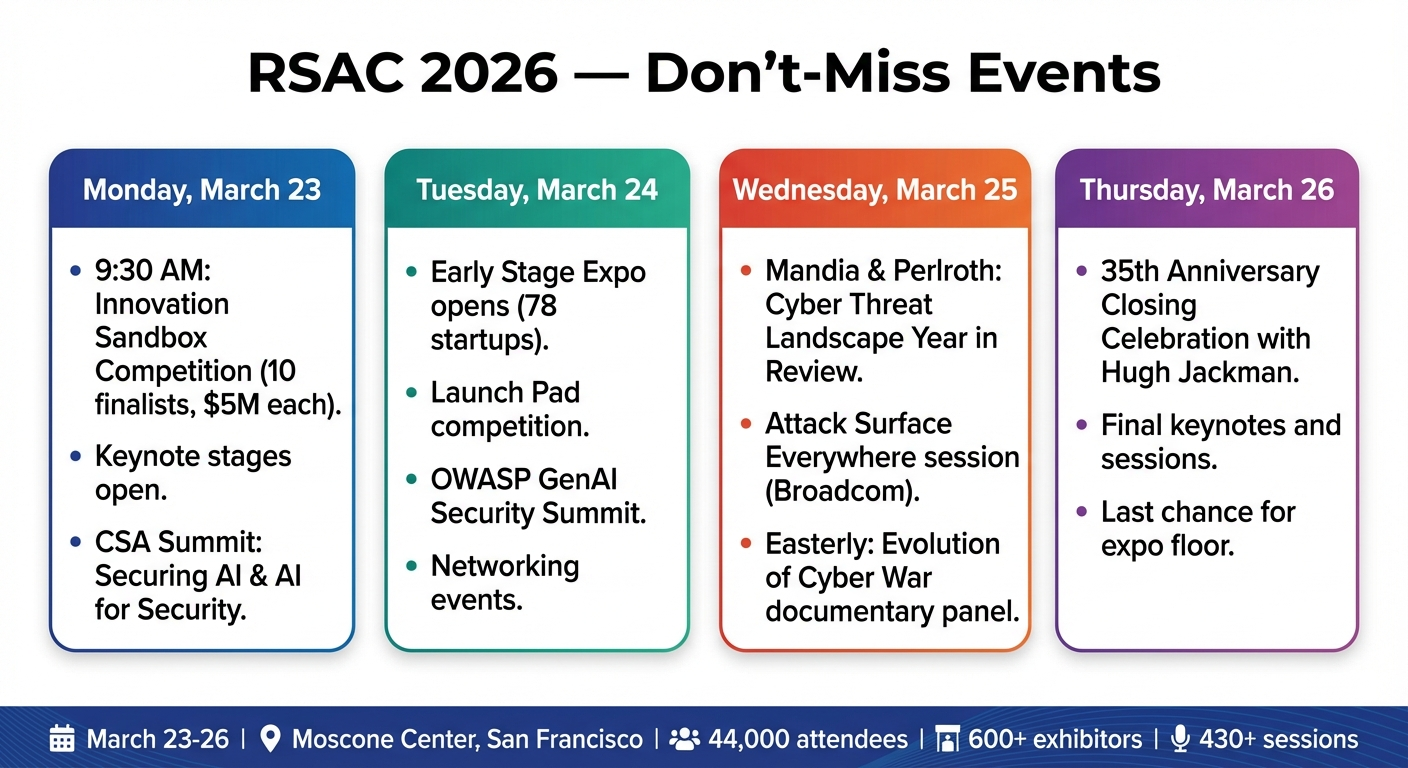
Having attended RSAC for years, I can say that this year feels different. Not because the expo floor will be bigger (it will — 600+ exhibitors and 78 early-stage companies), or because the keynotes will be more star-studded (Jacinda Ardern, Ben Horowitz, Michael Lewis, Adam Savage, and Hugh Jackman closing the 35th anniversary celebration). It feels different because the conversations have shifted from “what can AI do?” to “how do we architect security for a world where AI is the operating system?”
Here’s what I expect to see, what I’ll be paying attention to, and the themes I think will define cybersecurity for the next twelve months.
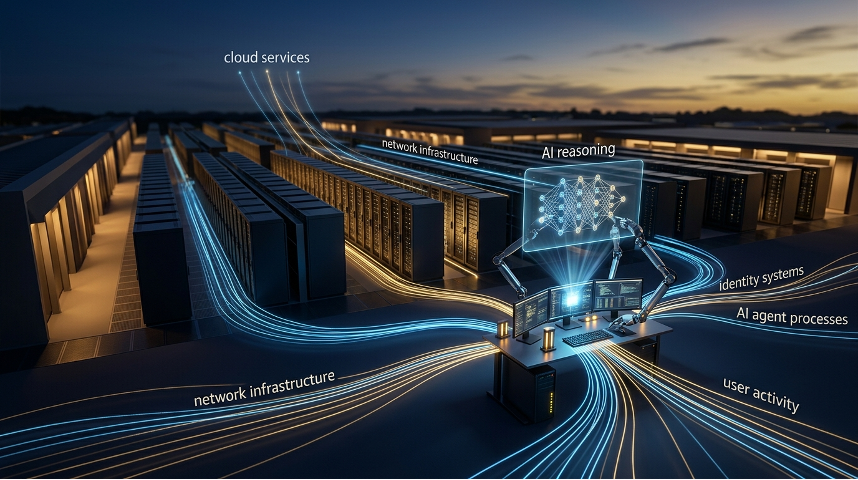
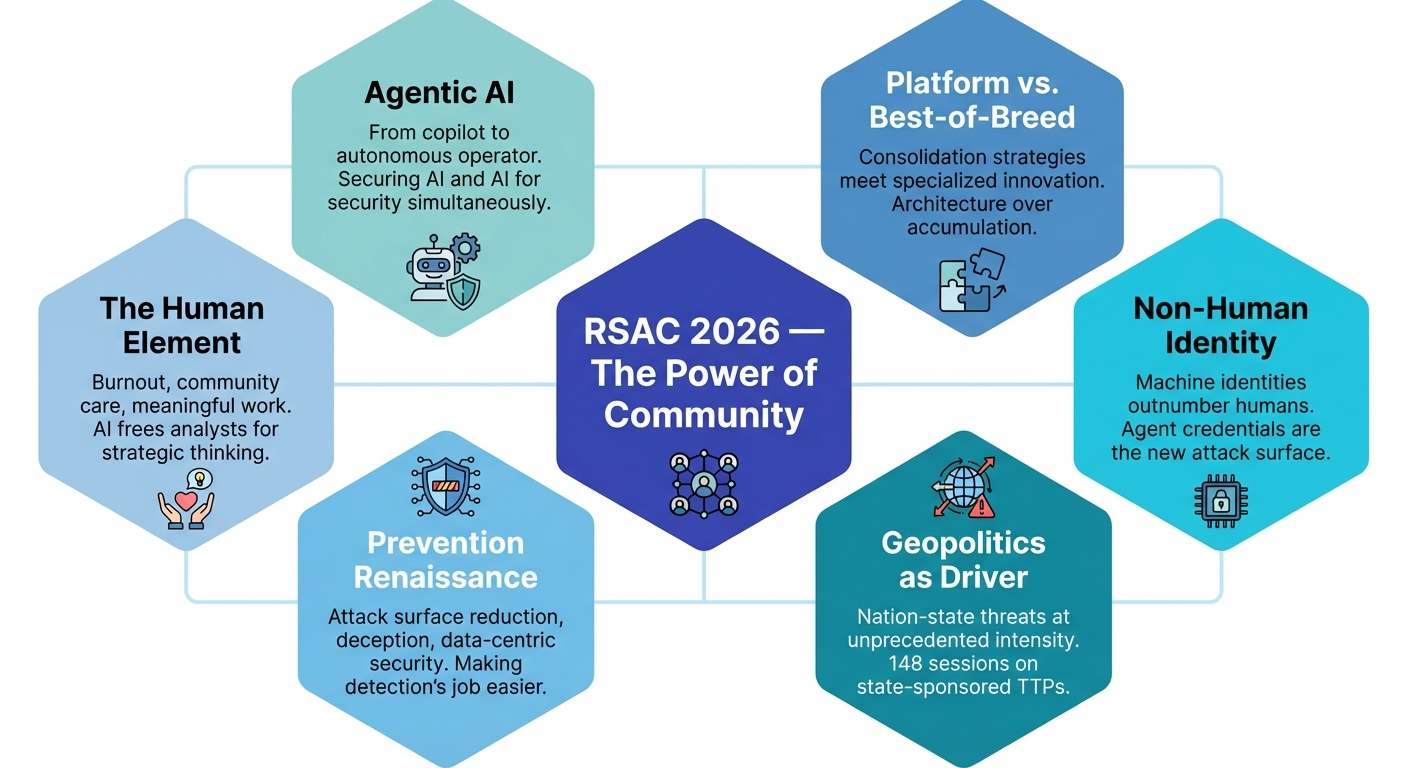
Agentic AI — From Copilot to Autonomous Operator
If last year’s RSAC was the “GenAI everywhere” conference, this year is the “agentic AI reckoning.” The shift is fundamental: we’re moving from AI as an assistant that summarizes and suggests to AI as an autonomous agent that plans, decides, and acts on its own.
RSAC’s own trend analysis of session submissions identified agentic AI and Model Context Protocol (MCP) as the two most dominant themes across hundreds of proposals. Microsoft’s pre-conference event is entirely organized around what they’re calling the “agentic era,” with sessions covering Agent 365, agentic defense architectures, and how to secure AI systems that operate with high privileges across enterprise environments. Gartner research cited at the conference warns that failing to implement robust AI governance will lead to 40% of AI-related data breaches stemming from agent misuse by 2027.
The security implications are profound and bidirectional.
On defense, agentic AI is transforming the SOC. AI agents that can autonomously triage alerts, correlate signals across data sources, enrich incidents with contextual intelligence, and execute containment playbooks represent the single most significant operational improvement in security operations in a decade. For understaffed security teams — which is nearly all of them — this is the difference between drowning in alerts and actually detecting threats. Expect every major platform vendor on the expo floor to be demonstrating some version of autonomous security operations.
On offense, agentic AI creates an entirely new attack surface. AI agents operating with high privileges across SaaS environments, cloud infrastructure, and internal systems present identity, access control, and data governance challenges that existing security architectures weren’t designed for. How do you manage the identity of an agent that operates 24/7, makes API calls across dozens of systems, and has access to sensitive data by design? How do you detect when an agent’s credentials have been compromised by a nation-state actor? These aren’t theoretical questions — they’re the questions multiple Innovation Sandbox finalists are building companies to answer.
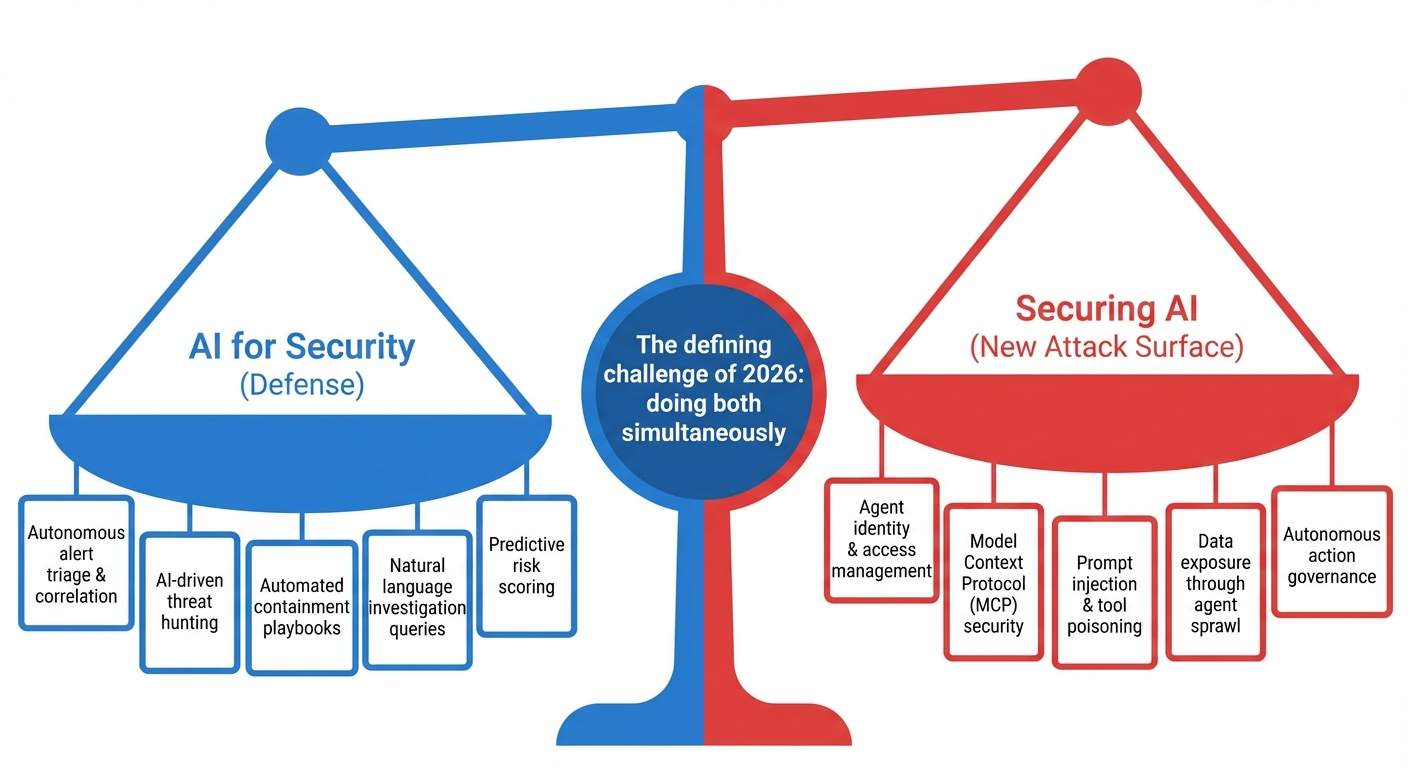
This is the year the industry has to grapple with both sides of that equation simultaneously — and the vendors that can articulate a coherent strategy for both will stand out from the noise.
Platform Consolidation vs. Best-of-Breed — The Debate Gets Real
For years, the “platform vs. point solution” debate has been largely rhetorical. This year, it’s operational. RSAC 2026 is shaping up to be the conference where consolidation strategies move from vendor pitch decks into actual deployment reality.
The driver is straightforward: the average enterprise juggles 83 security tools from 29 vendors, and most organizations report that their tools can’t be properly integrated. In a world where AI-driven SOC platforms need comprehensive telemetry to function effectively, and where agentic AI requires unified identity and policy frameworks, tool sprawl isn’t just an operational burden — it’s a strategic vulnerability.
Expect the major platform players — Microsoft, Palo Alto Networks, CrowdStrike, Cisco — to push hard on consolidation narratives. The message from the Broadcom/Symantec camp is particularly pointed this year: “single-agent platforms” as the disruptor to watch, with sessions explicitly arguing that fewer agents mean better outcomes with less operational overhead.
But here’s what I’ll be watching for: the counter-narrative from best-of-breed innovators who argue that consolidation creates single points of failure and that the real answer is interoperability, not monolithism. The Innovation Sandbox finalists — Charm Security, Clearly AI, Crash Override, Fig Security, Geordie AI, Glide Identity, Humanix, Realm Labs, Token Security, and ZeroPath — represent the sharpest edge of this argument. These companies are building highly specialized capabilities, from agentic AI fraud prevention to passwordless authentication to autonomous code security, that platforms can’t replicate with the same depth.
The truth, as usual, is more nuanced than either camp admits. The organizations I see getting security architecture right aren’t choosing platforms or point solutions — they’re building a telemetry-rich platform foundation and selectively layering specialized capabilities where the platform has gaps. The architecture decisions that matter aren’t about which vendor logo is on the dashboard; they’re about whether every layer of defense in depth is doing its job.
Identity Is the New Perimeter — And Non-Human Identity Is the New Frontier
Identity has been a major RSAC theme for several years running, but 2026 marks a qualitative shift. The conversation is no longer about whether identity is the new perimeter — that’s settled. It’s about the explosion of non-human identitiesthat now vastly outnumber human ones within enterprise environments, and the unique challenges they present.
Machine identities — service accounts, API keys, tokens, certificates, and now AI agent credentials — lack the same consistency of “logins” associated with traditional identity access management. AI agents further blur the lines between human and non-human identities, incorporating features of both. They operate autonomously, often with elevated privileges, across multiple systems and SaaS environments, making them extraordinarily attractive targets for adversaries.
This isn’t hypothetical. Nation-state actors are already targeting AI agent credentials to access internal applications and APIs. The Big Four adversaries understand that as organizations push more autonomy to AI agents, compromising those agents’ identities provides access that is persistent, high-privilege, and difficult to distinguish from legitimate automated activity.
RSAC 2026 will feature dedicated sessions on securing MCP, managing agent identity propagation across SaaS ecosystems, and building governance frameworks that can handle the scale and dynamism of non-human identity. Innovation Sandbox finalists like Token Security and Glide Identity are attacking this problem head-on, and vendors like CyberArk, DigiCert, and Delinea will be showcasing solutions for machine identity management and PKI-IoT integration.
For CISOs walking the floor, the question to ask every vendor isn’t just “how do you handle human identities?” — it’s “how do you handle the ten thousand machine identities that outnumber my humans, and the AI agents that behave like both?”
Geopolitics as a Cybersecurity Driver — The Wartime Conference
RSAC 2026 is likely to be remembered as the first true “wartime” RSAC. Operation Epic Fury is underway. The Typhoon campaigns are active. The DHS has issued multiple bulletins warning of heightened cyber threat. And notably, U.S. federal agencies have declined to participate at the conference this year, leaving an absence that the international community — including the UK’s NCSC CEO Richard Horne, UAE’s Dr. Mohamed Al Kuwaiti, and the European Commission’s Despina Spanou — is stepping in to fill.
With 148 sessions dedicated to nation-state threats and security strategies, geopolitics will permeate the conference floor. Kevin Mandia and Nicole Perlroth’s session, “The Cyber Threat Landscape: Year in Review, Future in Focus,” will likely draw one of the largest audiences of the week. Former RSAC CEO Jen Easterly is heading a panel connected to a new documentary, “Midnight in the War Room,” on the real heroes of cybersecurity. The overlap between kinetic conflict and cyber operations — a theme we are exploring in depth in our upcoming piece on the Big Four nation-state adversaries — will be front and center.
What I’ll be watching for is whether the industry moves beyond awareness into actionable architecture. We know China’s Volt Typhoon has been pre-positioned in critical infrastructure for five years. We know Iran’s Pioneer Kitten is collaborating with ransomware affiliates. We know Russia’s GRU-backed hacktivists are targeting exposed OT systems. The question isn’t whether these threats exist — it’s whether the solutions on the expo floor are actually designed to detect living-off-the-land techniques, protect operational technology environments, and respond at machine speed to adversaries who have already been inside the network for months.
Prevention Is Making a Comeback
Here’s a contrarian observation: after a decade of “assume breach” orthodoxy, prevention is re-emerging as a serious investment category at RSAC.
The prevention renaissance manifests in several ways across the RSAC agenda: attack surface management and reduction strategies, deception technology that makes environments hostile to adversaries before they trigger alerts, data-centric security approaches that make critical assets invisible or inaccessible to unauthorized processes, and Zero Trust architectures that enforce least-privilege access at every layer.
This is particularly relevant in the context of the AI SOC conversation. As we wrote in our earlier piece on the AI SOC and defense in depth, the AI SOC is the most powerful detection and correlation engine we’ve ever had — but it only works when the layers beneath it (telemetry foundation, prevention, attack surface reduction) and above it (human expertise, automated response) are functioning. Prevention reduces the signal-to-noise ratio for the detection layer, which makes the AI SOC more effective on the threats that actually matter.
The organizations that get the most out of their AI-driven detection investments in 2026 will be the ones that also invested in making sure fewer threats reach the detection layer in the first place.
The Human Element — Burnout, Community, and the Defender’s Experience
One of the most striking trends in RSAC 2026 session submissions was the volume of proposals addressing burnout — a signal that the community is ready to confront a crisis that has been building for years.
The cybersecurity workforce gap sits at 4.8 million unfilled positions. The people who are in the chairs are carrying impossible risk loads, often with inadequate tooling and insufficient organizational support. Sessions like “The Brutal Truth: 12 Critical Mistakes That Nearly Derailed My CISO Career” and “3 Ways CISOs Can Cut Team Burnout 25%+ in 90 Days” represent a culture shift — an acknowledgment that the community can’t secure organizations if it doesn’t take care of the people doing the work.
This connects directly to the AI transformation story. If agentic AI can genuinely automate Tier-1 triage, correlate signals without human intervention, and execute containment playbooks autonomously, the practical effect isn’t replacing analysts — it’s freeing them from the soul-crushing alert fatigue that drives burnout. The promise of the AI SOC isn’t fewer people; it’s people doing more meaningful work — threat hunting, strategic risk assessment, architecture design, and the creative, adversarial thinking that no model can replicate.
The “Power of Community” theme is the connective tissue here. The new Connection Hub at Moscone West, the expanded hands-on learning experiences, and the casual meetups and networking events are all designed around the principle that cybersecurity is fundamentally a team sport. The defenders win when they share intelligence, collaborate on standards, and build the kind of trust across organizations and borders that adversaries can’t match.
What I’ll Be Looking For on the Floor
Beyond the macro themes, here’s what I’ll be paying specific attention to as I walk the Moscone Center:
Innovation Sandbox (Monday, March 23). This is always the sharpest signal of where the market is heading. This year’s finalists — each awarded a $5M investment — span agentic AI fraud prevention (Charm Security), AI-assisted vulnerability remediation (ZeroPath), autonomous code security (Crash Override), and next-gen authentication (Glide Identity). The last 20 years of Innovation Sandbox finalists have seen over 100 acquisitions and $18.1 billion in investments. The Google-Wiz acquisition ($32 billion, from a 2021 finalist) still echoes. Watch what wins — it’s usually a leading indicator of the industry’s next major investment cycle.
Keynote conversations that move beyond hype. Mandia and Perlroth on the threat landscape. Easterly’s documentary screening on the real practitioners behind the headlines. Microsoft’s Vasu Jakkal on ambient, autonomous security. The international government voices — Horne from the UK NCSC, Al Kuwaiti from the UAE — filling the gap left by absent U.S. federal participation. And the 35th anniversary closing with Hugh Jackman, which promises to be equal parts celebration and reflection on how far the community has come.
The Early Stage Expo (78 startups). The most unfiltered signal of where founder energy is flowing. If you want to understand what the market will look like in three to five years, skip the mega-booths and spend two hours in the early stage section.
Sessions on OT/ICS security. Given the active targeting of operational technology by both Iranian and Russian actors, and China’s pre-positioning in industrial control environments, the sessions on Zero Trust for OT, ICS threat detection, and cross-domain convergence will be standing room only — and they should be.
The Takeaway for Security Leaders
If you’re a CISO, security architect, or practitioner heading to Moscone on March 23, here’s the framework I’d use to cut through the noise:
Prioritize sessions that are prescriptive, not descriptive. The threat landscape sessions are essential for context, but the sessions that will change your program are the ones offering concrete implementation guidance — how to segment OT, how to govern AI agent identity, how to build response playbooks that execute in minutes, how to reduce attack surface before the adversary arrives.
Build your network intentionally. The “Power of Community” theme isn’t just marketing. The connections you make at RSAC — the CISO who’s already deployed the agentic AI platform you’re evaluating, the incident responder who’s handled the exact TTPs you’re worried about, the startup founder who’s building the capability you can’t find anywhere else — are often more valuable than anything you’ll see on stage or in a booth.
And remember: no single tool is the whole answer. Not the AI SOC. Not endpoint security. Not data security. Not the platform consolidation play. Not the newest Innovation Sandbox winner. The answer is architecture — deliberately designed, layered, continuously evolved, and built around the specific threats your organization faces. That’s been true for thirty-five years of RSAC, and it’s more true today than ever.
See you at Moscone.
Brad Potteiger is the Chief Technology Officer at Arms Cyber, where he leads the development of next-generation preemptive security and anti-ransomware technology. Arms Cyber will be at RSAC 2026 — stop by to see how our patented Stealth Posture Management platform makes critical data invisible and resilient to attackers across Windows, Linux, and macOS, delivering prevention-layer security that reduces the burden on your detection and response stack