There’s a new protagonist in the cybersecurity story, and it’s hard to argue with its entrance. The AI-driven Security Operations Center — the “AI SOC” — has arrived with a compelling pitch: let machine intelligence handle the crushing volume of alerts, correlate signals across your environment in seconds, and triage incidents before a human analyst even opens their laptop. For security teams drowning in noise, it sounds like salvation.
And in many ways, it is. But salvation and invincibility are not the same thing. The AI SOC is a powerful, transformative layer in a modern security program. It is not, however, the entire program. And the organizations that treat it as one are setting themselves up for a painful lesson.
The problem the AI SOC actually solves
To appreciate where the AI SOC fits, you first have to understand the problem it was built to address. Security operations have been in crisis for years. The global cybersecurity workforce gap sits at roughly 4.8 million unfilled positions. The average enterprise manages 83 different security tools across 29 vendors. Alert fatigue isn’t a buzzword — it’s an operational reality where Tier-1 analysts spend their shifts closing false positives instead of investigating real threats.
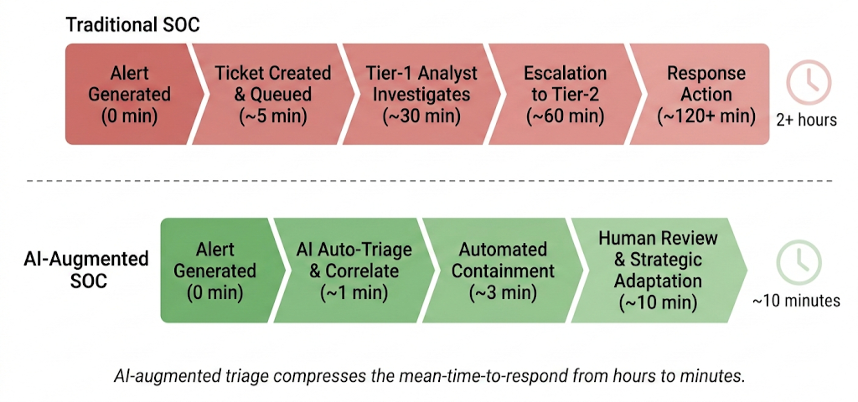
The traditional SOC model — generate alert, create ticket, queue for analyst, investigate, escalate, respond — was designed for a world where attacks moved at human speed. That world is gone. AI-accelerated offensive operations are compressing the attack chain from days to minutes. A manual triage pipeline that takes two hours to produce a response action is not just slow; it’s structurally incompatible with the threat landscape we’re entering.
The AI SOC attacks this problem directly. By automating Tier-1 triage, correlating signals across data sources, enriching incidents with contextual intelligence, and recommending or even executing response actions, an AI-driven platform can collapse that two-hour cycle into minutes. It doesn’t get tired. It doesn’t miss alerts at 3 a.m. It processes volume that would bury a human team. This is a genuine and significant operational advancement.
Where the AI SOC sits in defense in depth
Defense in depth is not a new concept. It’s the principle that no single security control should be trusted to stop every attack — instead, you layer complementary controls so that if one fails, the next catches what got through. What has changed is what those layers look like and what powers them. A modern defense-in-depth stack has roughly five functional layers, and the AI SOC occupies a critical — but specific — position within it..
At the foundation sits your product and telemetry layer: the deployed security tools that generate the raw data everything else depends on. Endpoint detection and response agents, firewalls, intrusion detection systems, identity and access management platforms, cloud security posture management tools. Without these products generating high-fidelity logs, alerts, and signals, there is literally nothing for any analyst — human or artificial — to work with. This layer is the bedrock.
Above that is prevention and attack surface reduction: hardening configurations, patching vulnerabilities, enforcing least-privilege access, deploying deception technologies that make your environment hostile to attackers before they ever trigger an alert. This layer’s job is to stop attacks from succeeding in the first place or to make the environment so uncertain that attackers waste time and reveal themselves.
Next comes the detection and correlation layer, and this is where the AI SOC lives. It ingests the telemetry from your product foundation, applies machine learning models and behavioral analytics to identify patterns that rule-based systems miss, correlates signals across endpoints, network, identity, and cloud, and produces prioritized, contextualized incidents instead of raw alert noise. This is where the AI SOC’s strengths are most transformative.
Above detection sits human expertise and judgment. Experienced analysts, threat hunters, incident responders, and security architects who provide the strategic thinking, contextual understanding, and creative problem-solving that AI cannot replicate. They interpret the AI SOC’s output, validate its conclusions, hunt for threats the models haven’t been trained on, and make the risk-informed decisions that shape the organization’s security posture.
Finally, the automated and orchestrated response layer executes containment, remediation, and recovery actions at machine speed — isolating compromised endpoints, revoking credentials, blocking malicious IPs, triggering playbooks — so that validated threats are neutralized before they spread.
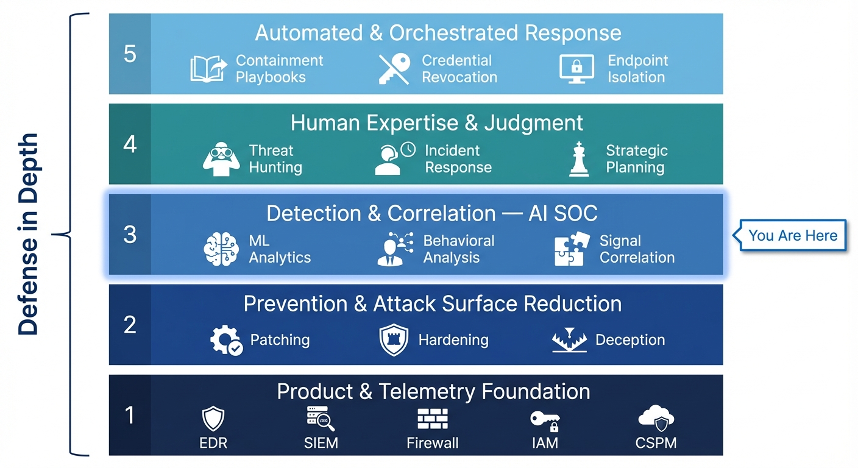
The AI SOC is the engine of the detection and correlation layer. It’s what makes that layer fast enough and scalable enough to keep pace with modern threats. But notice what it depends on and what sits above it. Without the telemetry foundation beneath it, the AI SOC is analyzing nothing. Without human expertise above it, the AI SOC’s output has no strategic context. Without prevention ahead of it, every attack reaches the detection layer, and no detection system — no matter how intelligent — catches everything.
What the AI SOC doesn’t do
This is the part of the conversation the industry tends to rush past, and it matters.
The AI SOC doesn’t prevent attacks. It detects and responds to them. That’s an essential distinction. An organization that invests heavily in AI-driven detection but neglects attack surface reduction — unpatched systems, over-permissioned identities, flat network architectures, exposed data — is relying on catching every punch instead of avoiding the fight. Behavioral detection is powerful, but it is inherently reactive: the malicious action has to begin before it can be observed.
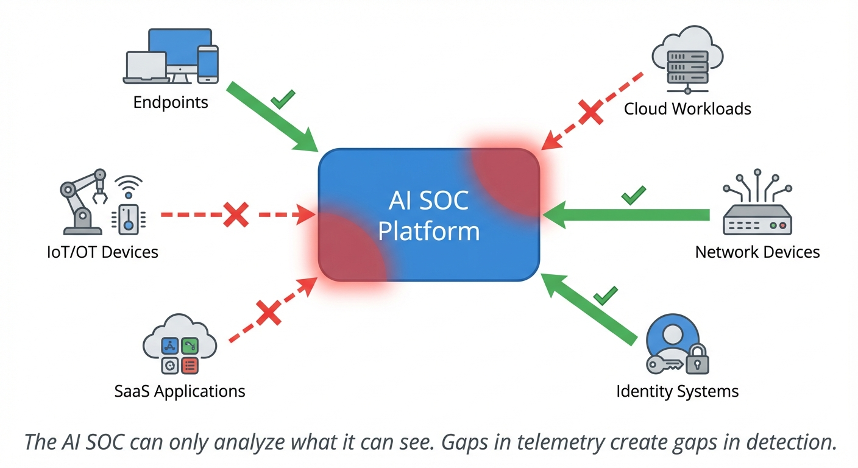
The AI SOC doesn’t generate its own data. It is entirely dependent on the quality, breadth, and fidelity of the telemetry flowing into it. If your endpoint agent isn’t deployed on 30% of your fleet, or your cloud workloads aren’t instrumented, or your identity logs aren’t flowing into the platform, the AI SOC has blind spots that no amount of algorithmic sophistication can overcome. Silence in, silence out.
The AI SOC doesn’t replace human judgment. It augments it. AI models are trained on known patterns, and they’re increasingly good at identifying novel variations of those patterns. But genuinely novel attack techniques — the zero-days, the creative abuse of legitimate tools, the social engineering campaigns that never touch a technical control — still require human intuition, experience, and contextual reasoning to identify and address. The AI SOC’s role is to free human analysts from the grunt work so they can focus on the problems that actually require their expertise.
The AI SOC doesn’t harden your environment. It doesn’t patch your systems, enforce MFA, segment your network, or reduce the blast radius of a compromised credential. Those are prevention-layer responsibilities, and they’re the controls that determine how much work the detection layer has to do in the first place. The less that gets through your preventive controls, the more effective your AI SOC can be on the threats that truly matter.
The defense-in-depth imperative
The risk I see most often is what I’d call “detection-layer overconfidence.” An organization deploys an AI SOC platform, sees immediate value in reduced alert noise and faster triage, and concludes that the detection problem is solved. Investment in other layers stalls. Prevention gets deferred because “the AI will catch it.” Telemetry gaps go unaddressed because the dashboards look clean. Human analyst headcount gets cut because “the AI handles Tier-1 now.”
This is the cybersecurity equivalent of removing your seatbelt because your car has airbags. Airbags are genuinely life-saving — but they work best when they’re one part of a comprehensive safety system, not a substitute for it.
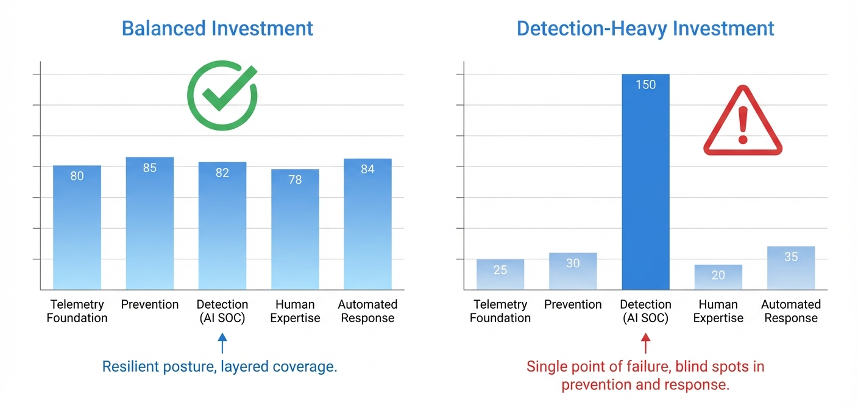
Defense in depth works because it’s designed for failure — not in a pessimistic sense, but in an engineering sense. Each layer assumes the layer before it will occasionally fail, and it’s designed to catch what gets through. The AI SOC is the most powerful detection and correlation engine we’ve ever had. But it needs a strong product foundation feeding it data, a robust prevention layer reducing the volume of threats it has to process, skilled humans interpreting its output and hunting for what it misses, and automated response capabilities executing containment at machine speed.
Getting the architecture right
If you’re evaluating an AI SOC platform — or if you’ve already deployed one — the question to ask isn’t “does this solve my security problem?” It’s “does this fit into an architecture where every layer is doing its job?”
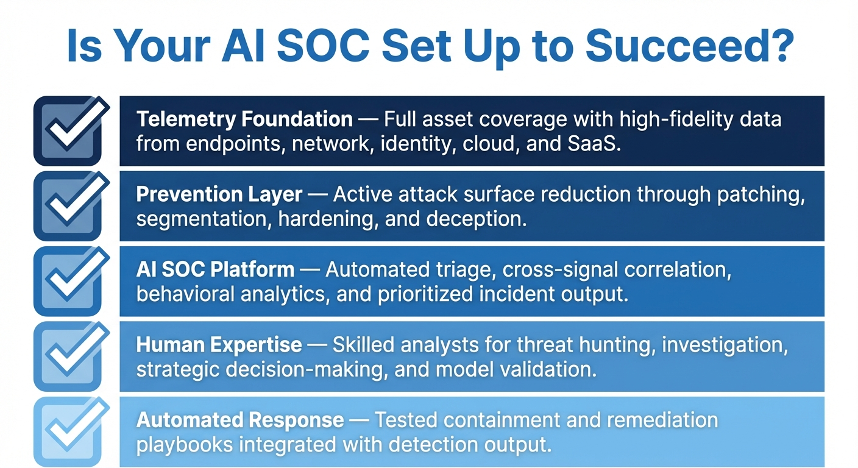
Start with your telemetry foundation. Map your asset inventory against your deployed security products and identify the gaps. If the AI SOC can’t see your cloud workloads, your SaaS applications, or your OT environment, those are invisible attack surfaces.
Invest in prevention independently of detection. Patch management, identity hygiene, network segmentation, deception technology, and data-centric security controls like making sensitive files invisible to unauthorized processes all reduce the burden on your detection layer and shrink the blast radius when something does get through.
Treat the AI SOC as your detection force multiplier, not your entire detection strategy. Layer it with threat intelligence, periodic red team exercises, and human-led threat hunting to catch what the models miss.
Retain and develop human expertise. The AI SOC doesn’t eliminate the need for skilled analysts — it changes what they spend their time on. The organizations that cut analyst headcount in response to AI-driven triage automation will find themselves without the strategic and investigative capability they need when a sophisticated adversary gets through.
And build automated response playbooks that are tested, maintained, and integrated with your AI SOC’s output. Detection without response is just expensive observation.
The bottom line
The AI SOC is one of the most important advancements in cybersecurity operations in a decade. It solves real problems — alert fatigue, analyst shortages, triage speed — that have plagued the industry for years. It deserves the investment and attention it’s getting.
But it is one layer in a defense-in-depth architecture that requires every layer to function. It’s not a substitute for comprehensive telemetry, proactive prevention, human expertise, or automated response. It’s the component that makes the detection layer fast enough and smart enough to keep pace with AI-accelerated threats — and that’s a big deal. But “a big deal” and “the whole deal” are very different things.
The organizations that will be most resilient aren’t the ones that deployed the flashiest AI SOC. They’re the ones that built the architecture around it to make it effective — and that continue to invest in every layer of the stack, not just the one that’s generating the most buzz.
Brad Potteiger is the Chief Technology Officer at Arms Cyber, where he leads the development of next-generation preemptive security and anti-ransomware technology. Arms Cyber’s patented Stealth Posture Management platform protects organizations across Windows, Linux, and macOS by making critical data invisible and resilient to attackers.