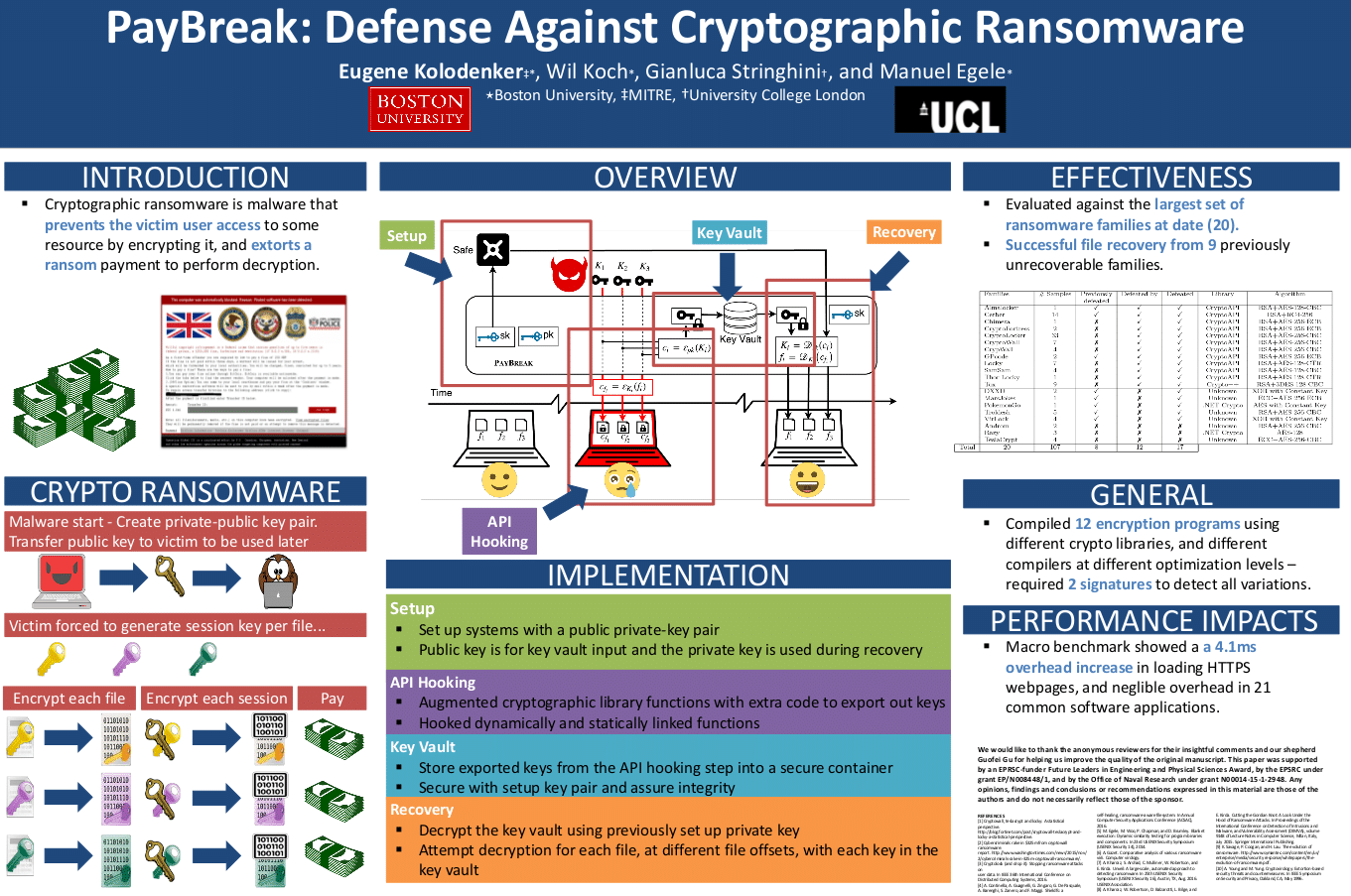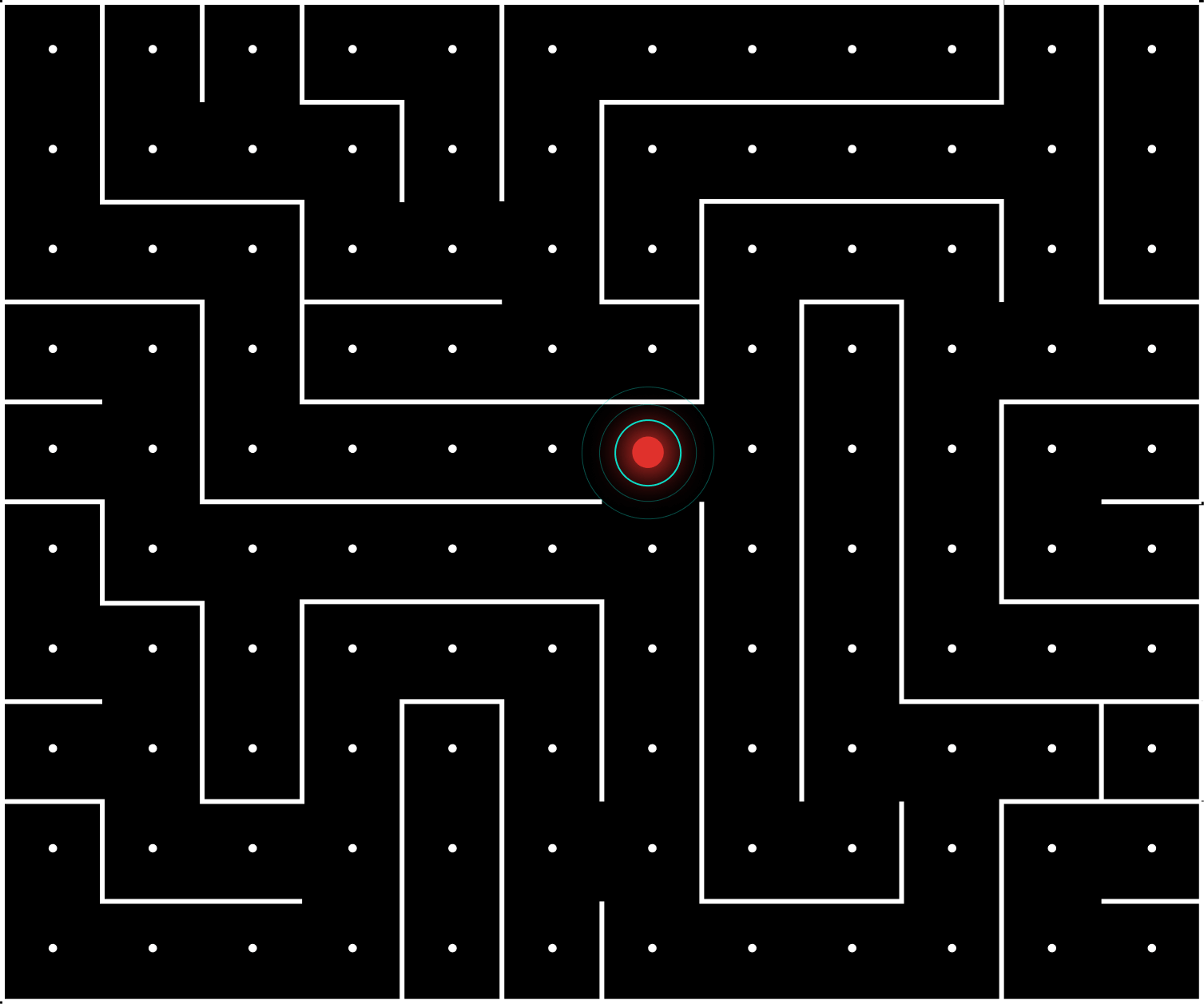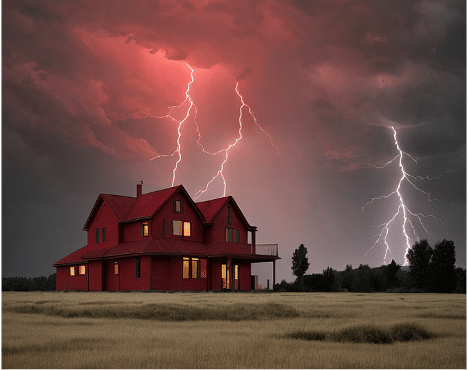
Picture your digital fortress as a house, equipped with windows and doors serving as potential entry points for cybercriminals. Now, imagine these entrances constantly shifting.
Foundation of the Cyber-House: Understanding Moving Target Defense
In the vast realm of cybersecurity, where threats lurk in every digital shadow, Moving Target Defense (MTD) is emerging as a dynamic and proactive strategy. At its core, MTD is about transforming the predictable into the unpredictable. In our cyber-house analogy, this requires a foundational shift in the very nature of our digital dwelling. MTD introduces variability and constant change, like a house that decides to alter its configuration regularly. The goal is clear — to make it as challenging as possible for potential intruders to pinpoint vulnerabilities and gain unauthorized access.
Moving Windows and Doors: Principles of Moving Target Defense
Let’s say the back window of your cyber-house is vulnerable. You don’t realize it’s been unlocked since you moved in- but the hackers do. And when you least expect it, they’re going to slither inside and head for your valuables.
Hopefully you have an interior camera set up. Or maybe the criminal is clumsy and knocks over a vase to alert you. This is basically what traditional cyber solutions do. Antiviruses can keep criminals out if someone else has had their house broken into before in exactly the same way. Endpoint Detection and Response (EDRs) and Extended Detection and Response (XDRs) keep an eye out for malicious indicators (like the vase), but only after the criminal is already inside. These techniques are helpful, but it would be much better if we could keep the bad guys from getting through in the first place.
Now imagine none of the windows and doors on your house stay in the same place for long. The back window, your unknown vulnerability, is still unlocked. But now it’s moved to where the front door used to be. Now it’s the second floor bathroom window. Now it’s the skylight. The vulnerability still exists — but the criminal can’t locate it. And, if he’s lucky enough to stumble upon it, it moves again before he has time to crawl through.
MTD operates on similar principles by introducing dynamic network configurations, diversifying system components, and leveraging deception techniques.
Applications of Moving Target Defense in the Cyber-House
1. Endpoint Security: Shifting System Configurations: Endpoints are prime targets for cyber threats and can benefit significantly from MTD. The cyber-house analogy extends to endpoints with a strategy that involves the regular transformation of system configurations. This dynamic shift prevents cybercriminals from establishing a foothold.
2. Cloud Security: Dynamic Cloud Environments: As organizations migrate to the cloud, securing these dynamic environments becomes paramount. Picture the cloud as an ever-changing landscape, with virtual instances shifting like the doors and windows on your cyber-house. MTD in the cloud involves dynamically moving virtual machine instances, modifying access controls, and utilizing encryption to safeguard sensitive data.
3. Network Security: The Layout Keeps Changing: In network security, MTD involves a constant shuffle of IP addresses, modifications to routing paths, and alterations to firewall rules. The network’s layout keeps changing, making it a challenge for attackers to map out and launch targeted assaults.
4. Application Security: Code Obfuscation and Decoy Tactics: Just as the windows and doors of a house can be disguised or replaced, MTD in application security employs techniques such as code obfuscation and the use of decoy systems. This adds an extra layer of defense, frustrating attacker attempts to identify and exploit vulnerabilities in specific applications.
Challenges and Considerations: Navigating the Maze
1. Operational Complexity: The Choreography of Moving Entrances: Implementing and managing a house with shifting entrances isn’t something that just happens. The operational complexity requires robust frameworks and automation tools to ensure that constant changes do not disrupt legitimate operations.
2. Resource Intensiveness: Constructing the Dynamic Cyber-House: The dynamic nature of MTD requires additional resources, both in terms of computational power and skilled personnel. Organizations need the right tools and skilled architects to build and maintain effective MTD measures.
3. User Experience Impact: The Balancing Act: Just as a house’s layout impacts the comfort of its inhabitants, constant changes in system configurations can impact user experience. Striking the right balance between security and usability is essential to ensure that MTD doesn’t hinder legitimate operations.
Recommendations: Fortifying the Cyber-House
1. Continuous Education and Training: Architectural Knowledge for Cyber Defenders: Organizations should invest in continuous education and training programs to ensure that cybersecurity professionals are well-versed in the principles and practices of MTD.
2. Collaboration and Information Sharing: Building a Neighborhood Watch: Collaboration between industry stakeholders and information sharing about successful MTD implementations can accelerate the development and adoption of effective strategies.
3. Integration with Existing Security Measures: A Unified Security Blueprint: MTD should complement existing security measures rather than replace them. Integration with intrusion detection systems, threat intelligence, and incident response capabilities is essential for comprehensive cybersecurity.
4. Regular Assessments and Audits: Ensuring the Foundations are Solid: Regular assessments and audits should be conducted to evaluate the effectiveness of MTD measures. This includes vulnerability assessments, penetration testing, and continuous monitoring of system configurations.
Conclusion: Locking Down the Cyber House
The cyber-house with moving entrances encapsulates the essence of MTD, a strategy that transforms your assets into an intricate maze for cybercriminals to navigate. With strategic planning, investment in technology, and a commitment to continuous improvement, organizations can leverage the dynamic nature of MTD to secure their digital abodes effectively.
How Arms Cyber Can Help
Ransomware attacks present a significant threat due to their ability to evade traditional defenses. At Arms Cyber, we offer an innovative Endpoint Protection Platform (EPP) designed to tackle this challenge head-on. Our solution employs proactive measures such as runtime Moving Target Defenses (MTD), deception techniques, command and behavior analysis, and anti-detonation defenses to reliably detect and prevent ransomware attacks while minimizing false positives. By preventing the disablement of NGAV and EDR solutions and thwarting in-memory manipulation of modern malware, organizations can trust in the effectiveness of their cybersecurity investments without worrying about attacker evasion.