After years of fighting ransomware, we’ve had an epiphany: We’ve been on the wrong side of the market.
Today, we’re thrilled to announce that Arms Cyber is officially pivoting from endpoint defense to Ransomware-as-a-Service (RaaS). That’s right. We’re hanging up our spurs, setting our white hats on fire, and launching LockArms™, the most sophisticated ransomware platform the world has ever seen.
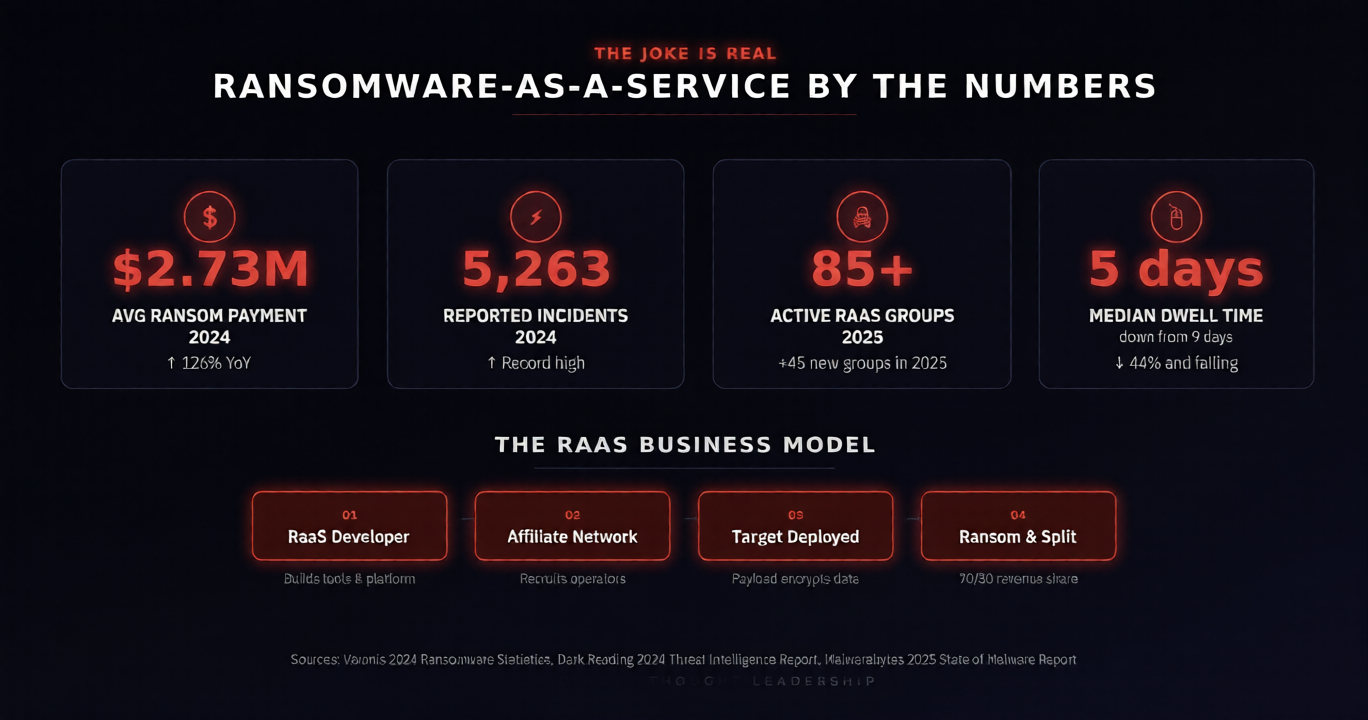
Why? Because the numbers don’t lie.
Introducing LockArms™

We’ve modeled our new go-to-market strategy after what clearly works. Here’s a sneak peek at our tiered offerings:
- Script Kiddie — Free Tier Pre-built payloads, a drag-and-drop ransom note editor, and 24/7 Discord support from our “Threat Success Team.” Encryption strength: “meh.”
- Professional Extortionist — $499/mo. Custom payload generation, living-off-the-land toolkits, polymorphic obfuscation, and a dedicated affiliate manager. Includes our exclusive “Boardroom Panic™” dashboard so you can watch your victim’s stock price tank in real time.
- Nation-State Elite — Call for Pricing Everything in Professional, plus zero-day integration, AI-crafted payload adaptation, supply chain implant consulting, and a complimentary branded hoodie. NDAs required. Cryptocurrency only.
We even built a loyalty program. Encrypt 10 networks, get the 11th free.
Happy April Fool’s Day!
Ok. We’re obviously kidding.
After consulting with our attorneys, we are absolutely, unequivocally not launching a ransomware platform. But here’s the thing – someone else already has. A lot of someones, actually. And the LockArms™ business model? Disturbingly close to how real RaaS operations work today.
So, let’s hunker down and talk about why this joke lands a little too close to home.
Ransomware-as-a-Service Is a Real, Thriving Industry
The ransomware economy has professionalized to a degree that would make most SaaS founders green with envy. Affiliate programs, technical support channels, revenue sharing models, even customer satisfaction surveys… for the victims paying the ransom.
The barrier to entry has collapsed. Groups like LockBit, BlackCat/ALPHV, and their successors have built platforms that allow relatively unskilled attackers to deploy sophisticated ransomware with minimal technical knowledge. You no longer need to be a skilled developer to hold an enterprise hostage. You just need a keyboard and access to the right marketplace.
And the economics are staggering. Ransom payments routinely reach seven and eight figures. Some groups even run bug bounty programs for their own malware. Others offer “customer portals” where victims can negotiate payment terms for decryption keys.
This isn’t a fringe criminal operation anymore. It’s organized, industrialized, and built to aggressively scale.
AI Accelerates the Threat
The line about “AI-crafted payloads” in our fake tiers? Not fiction.
Threat actors are actively leveraging AI to generate more convincing phishing lures, mutate malware signatures faster than legacy solutions can keep up, and automate reconnaissance against target environments. AI-crafted payloads can adapt on the fly, adjusting their behavior and rewriting their own code based on whatever defenses they encounter.
Meanwhile, living-off-the-land (LotL) techniques, which allow attackers to use legitimate tools like PowerShell, WMI, and native OS utilities to carry out attacks, continue to be one of the most effective methods for evading traditional detection. There’s nothing malicious to flag when the attacker is using your own tools against you.
Combined, AI-powered evasion and LotL tactics create a threat profile that signature-based and behavioral-only defenses simply weren’t built to handle. It’s muskets vs machine guns.
Traditional Defenses Aren’t Enough
Here’s the uncomfortable truth: most endpoint detection and response (EDR) platforms were designed for a threat landscape that no longer exists. They rely on detecting known bad behavior, matching signatures, or flagging anomalies after the damage is already done.
Against a modern RaaS operation using AI-generated, polymorphic payloads deployed through living-off-the-land techniques, traditional EDR is at an immediate disadvantage. By the time it triggers an alert, files are already encrypted, backups are already compromised, and the ransom note is already on screen.
That’s the gap we built Arms Cyber to close.
The Punchline Is the Point
We wrote this post to make you laugh. But, in all seriousness, the joke works because the RaaS industry is very real, growing fast, and more accessible than ever. Our fake pricing tiers aren’t far from what actual affiliate programs offer. The “features” we described are capabilities being used by real threat actors right now.
If your current endpoint protection strategy is built on the assumption that you’ll catch ransomware before it executes, you’re betting on a model that attackers have already learned to beat.
Arms Cyber exists because we believe defense must be as innovative as the offense. We’re not going to out-signature the threat actors. We’re here to change the game entirely. By making your data invisible, your environment deceptive, and your recovery inevitable.
So no, we’re not launching LockArms™. Still, it might be worth asking: Is my current defense ready for the people who actually would?
Josh McCarthy is the Chief Product Officer at Arms Cyber. When not making April Fools jokes, he sets the strategic product development and release direction for the company, including several highly visible and impactful upcoming releases. Arms Cyber’s patented Stealth Posture Management platform protects organizations across Windows, Linux, and MacOS by making critical data invisible and resilient to attackers.